Table of Contents
Updated on 2022-12-23: Okta GitHub Repositories Breached
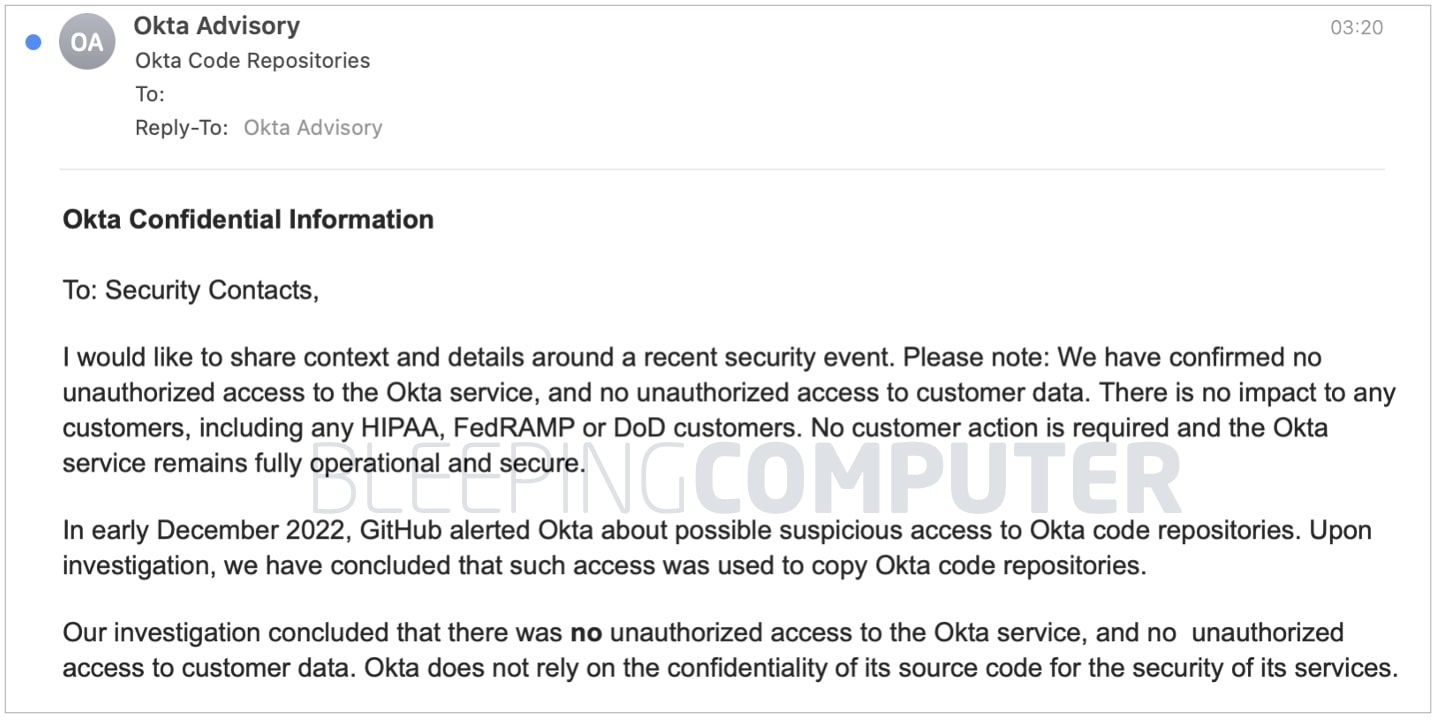
Single sign-on management company Okta says that intruders accessed their GitHub repositories and copied source code for Okta Workforce Identity Cloud service. Okta learned of the incident from GitHub, which notified Okta of “suspicious access” to its repositories in December. Okta officials said, “there was no unauthorized access to the Okta service, and no unauthorized access to customer data.”
Note
- This should be a non-event. Attackers in possession of the source code will not be able to do anything a responsible vendor has not already done as part of their software quality assurance process. Manual and automatic code reviews, dynamic testing assisted by full insight into the source code should be easier for the vendor creating the code than for a third party attacker. On the other hand, we are talking about a vendor producing critical security software.
- There is an old saying “If you put all your eggs in one basket, watch that basket really, really carefully.” Password managers and SSO platforms are essential big baskets of eggs full of passwords and are obvious high leverage targets for attackers. Both Last Pass and Okta have had serious breaches (even if no customer data was exfiltrated) recently – they haven’t been watching their (your) baskets carefully enough. At renewal time for all such services, require information on security changes and testing and consider competitive procurements.
- When first discovered, Okta shut down access to their GitHub repositories, and after analyzing access, has since restored that access. The exposure was specific to their new Workforce Identity Cloud service which provides access management, governance and privileged access controls in one package. The attackers are claiming they had sufficient access to reset passwords and MFA credentials data for Okta customers while Okta claims they were not. This follows the August breach of Twilio (used for SMS validation) and September breach of recently acquired Auth0. While the issue of who has which data is being sorted out, you may want to consider what options you have, including changing credentials, use of SMS validation and moving to another solution, just in case.
- Single sign-on and password managers are the old solution to part of the password problem. While better than nothing, they are still limited. Passkeys are the modern solution. They offer both safety and convenience. Be sure to offer this option to your users. Three months might be a reasonable schedule.
- It appears that cyber criminals [or nation states] are ‘upping’ their game by attacking companies that centralize critical information. In this case company proprietary information was lost that could be used to find and exploit vulnerabilities in the Workforce Identity Cloud service. Companies that offer consolidation/centralization services, should revisit their security processes and make it a regular discussion item as part of board level risk management.
Read more in
- Okta Code Repositories
Updated on 2022-12-22: GitHub/Heroku/TravisCI security incident
Okta told customers that a threat actor gained access to its GitHub repositories and stole some of its source code. This incident is actually part of a larger set of GitHub account intrusions that took place earlier in December. At the time, threat actors used Heroku and TravisCI integrations to access GitHub accounts in an incident similar to one that happened earlier in the year, in April. GitHub has not returned a request for comment.
Overview: Okta’s source code stolen
Okta confirmed that its private GitHub repositories were hacked this month and threat actors stole the source code.