Updated on 2022-12-28
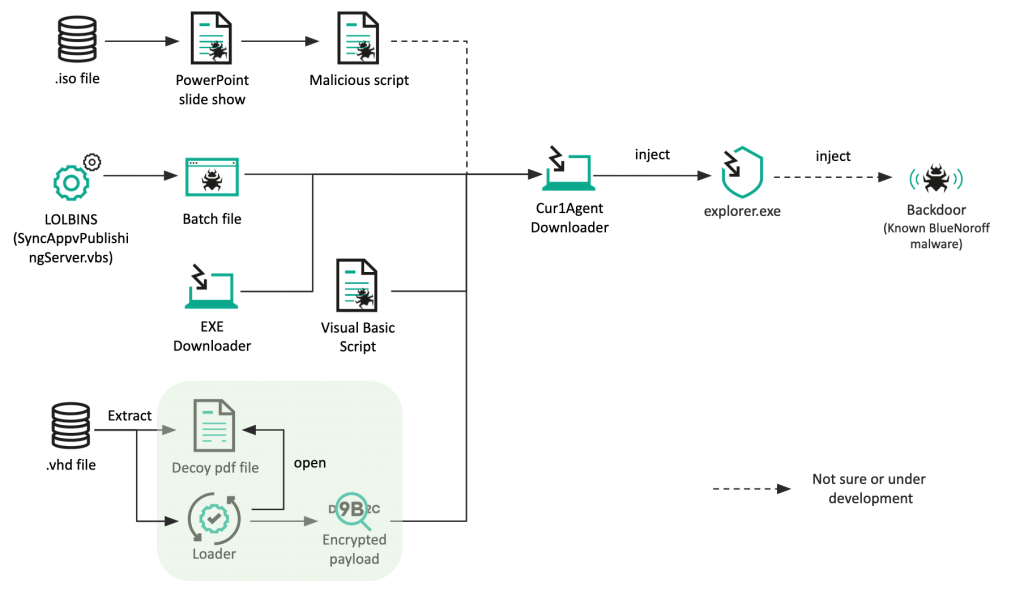
Kaspersky has an analysis of recent MOTW bypass techniques used by the BlueNoroff North Korean APT in attacks since this September. This includes hiding malware inside ISO or VHD files and the use of Batch scripts and various LOLbins.
Overview
The financially motivated BlueNoroff group was found using a new malware strain to target financial institutions in Japan. The gang has also devised a new tactic to evade Mark-of-the-Web (MotW) security measures. Read more: BlueNoroff introduces new methods bypassing MoTW