Table of Contents
Updated on 2023-01-02: PyTorch-nightly Dependency Chain Compromised
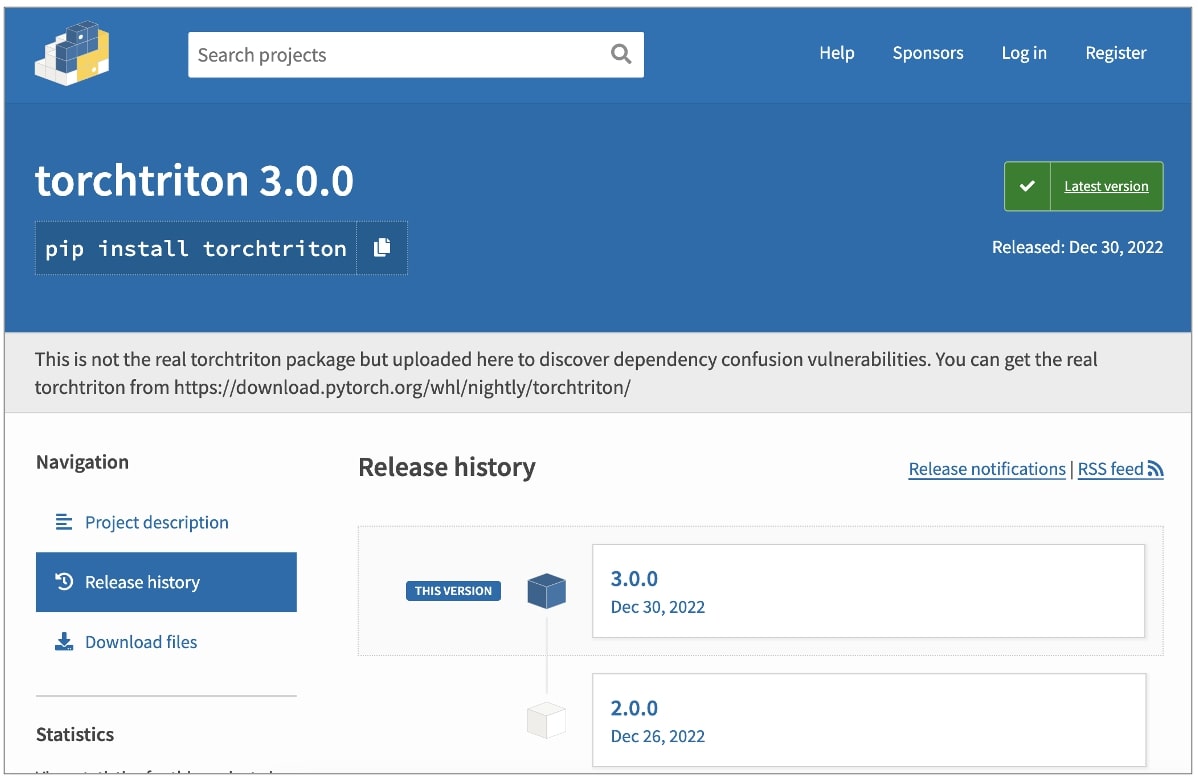
Machine learning framework PyTorch has disclosed that the PyTorch-nightly dependency chain was compromised in late December. Users who installed PyTorch-nightly Linux packages with pip between December 25 and 30 should uninstall those nightly builds and use the most recent nightly binaries. The dependency in question, torchtriton, was compromised on the Python Package Index (PyPI) code repository.
Note
- Luckily, this only affected the “nightly” builds and only a specific set of features of this very popular machine learning framework. But the event yet again shows the problematic state of the Python supply chain if even major and actively maintained packages can be affected by the compromise of a “random” Python package.
- Note this only impacts the nightly-build (vs stable) versions of these packages. Make sure you uninstall all four packages (torch, torchvision, torchaudio & torchtriton) as well as purge your cache for these before loading the updated binaries. The bad version of torchtriton was uploaded with the same package name as the nightly-build version, and due to the PyPi index taking precedence, the bad version was loaded versus the official version. The PyTorch team has renamed the torchtriton dependency to pytorch-triton as well as reserving a dummy package to prevent future attacks.
Read more in
- Compromised PyTorch-nightly dependency chain between December 25th and December 30th, 2022.
Updated on 2023-01-01
PyTorch detected a malicious dependency with the same name as the framework’s torchtriton library. It led to a successful chain compromise via the dependency confusion attack vector.
“Please uninstall it and torchtriton immediately, and use the latest nightly binaries (newer than Dec 30th 2022),” advises PyTorch team.
Overview: PyTorch supply chain incident
The team behind the PyTorch machine learning library said it discovered a supply chain attack that impacted its nightly builds on Linux. Between December 25, 2022, and December 30, 2022, a previously safe dependency named “torchtriton” turned malicious and installed a binary that could collect system information and read sensitive files, the team said.