An individual claiming to be a former member of the URSNIF malware operation has leaked the real-world identities of three of the gang’s members in a series of tweets last week.
The account, going by the name of URSNIFleak, has also released snippets from the gang’s internal chats, along with screenshots of some of the URSNIF malware’s source code and private messages sent via an underground malware forum, discussing topics like money laundering and the war in Ukraine.
The incident marks the fourth major doxing of a cybercrime operation this year after similar leaks exposed crucial and very sensitive information about the operations of the Conti ransomware, the TrickBot trojan, and the Yanluowang ransomware gang.
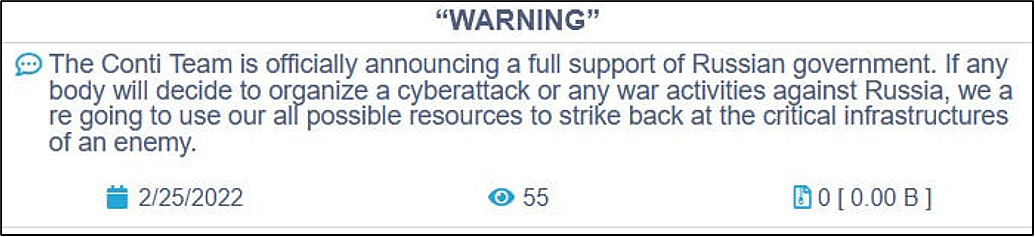
The first two leaks were driven by an anti-Russian sentiment as the Conti gang (which also managed the TrickBot botnet) showed their support for Russia’s brutal invasion of Ukraine. The reasons for the Yanluowang leak are still unknown.
However, the reason behind the URSNIF leak is much more mundane—and it’s revenge and your run-of-the-mill extortion.
The leak was teased over several days (on a first now-suspended Twitter account); they first leaked details of low-level members to show they were serious;
And the URSNIFleak account stopped posting new content after the leader of the URSNIF gang (an individual named CAP) paid them off to keep quiet.
“I just made more money in a single week than I have made in years. Pay workers right and they wont have a reason to leak s***,” URSNIFleak wrote in their last tweet before allegedly closing the account.
In another tweet, URSNIFleak said they decided to go through with the leak and extortion after reading statements made by the URSNIF leader in a recent interview with the VX-Underground project. What particular part, they did not say.
“The interview angered me,” URSNIFleak said. “He has been a bad boss for a long time. I have been waiting for the right time to release.”
Compared to the Conti, TrickBot, and Yanluowang leaks, less information was released in the URSNif dox, but despite this, nobody in infosec is complaining. More cybercrime leaks, plz! Especially leaks like these that show how URSNIF’s recent pivot to a ransomware operation was not as successful as the gang was hoping.