Table of Contents
- Updated on 2023-01-11
- SF BART ransomware
- OxShag leak
- DNV ShipManager attack
- Cryptome suspension
- Windows 7 end of extended support
- DDoS attacks on Serbian govt
- Malta drops Huawei CCTV project
- DNS4EU
- US Supreme Court denies NSO Group
- DOI password audit
- Auction site scammer sentenced
- New npm malware
- Dark web drug markets
- ScrubCrypt
- Godfather in Germany
- Lorenz ransomware update
- Kinsing attacks
- URSNIF
- Raspberry Robin partial takedown
- PlugX analysis
- Hive’s XDR33 variant
- StrongPity APT
- Threema vulnerabilities
- $1 million bounty
- Experian website bug
- Taking over a dead IoT company
- CVE-2022-23529
- CVE-2022-43974
- Asus router vulnerabilities
- Siemens PLC vulnerabilities
- Patch Tuesday
- New tool—ImageMagick Security Policy Scanner
- New tool—cobalt-strike-stager-parser
- Red Hat Insights
- Updated on 2023-01-10
- More highlights from the past 24 hours
- Updated on 2023-01-09
- More highlights from the past 24 hours
- Updated on 2023-01-08
- Chick-fil-A security incident
- AirFrance-KLM incident
- Ray-Ban lawsuit
- WhatsApp gets proxy support
- Apple fined in France
- Louisiana porn law
- DDoS attack on Danish Army
- Cyber-attacks on Moldova
- Wikipedia’s Saudi Arabia scandal
- Rogue Dutch govt employee
- Ransomware investigation
- NSO update
- C&C server list
- eBPF malware usage
- Mac ransomware
- Mac malware of 2022
- New ransomware
- Automated Libra’s PurpleUrchin
- Dridex update
- poweRAT
- BlueBottle
- SpyNote leak
- BlindEagle APT
- Rattlesnake APT
- Saaiwc Group
- Kimsuky APT
- Cold River APT
- Turla APT
- ReDoS beg bounties
- AWS keys on PyPI
- OWASSRF, TabShell
- CVE-2022-43931
- CVE-2022-47523
- CVE-2022-39947
- New tool—Hardeneks
- Updated on 2023-01-07
- Rackspace blames zero-day for ransomware hit
- Cops hacked thousands of phones. Was it legal?
- First LastPass, now Slack and CircleCI have confirmed hacks
- Russian hackers targeted U.S. nuclear scientists
- How do you know when macOS detects and remediates malware?
- The revamped NSA museum opens with displays of former nuke secrets and spy artifacts
- Guardian shutters office after ransomware attack
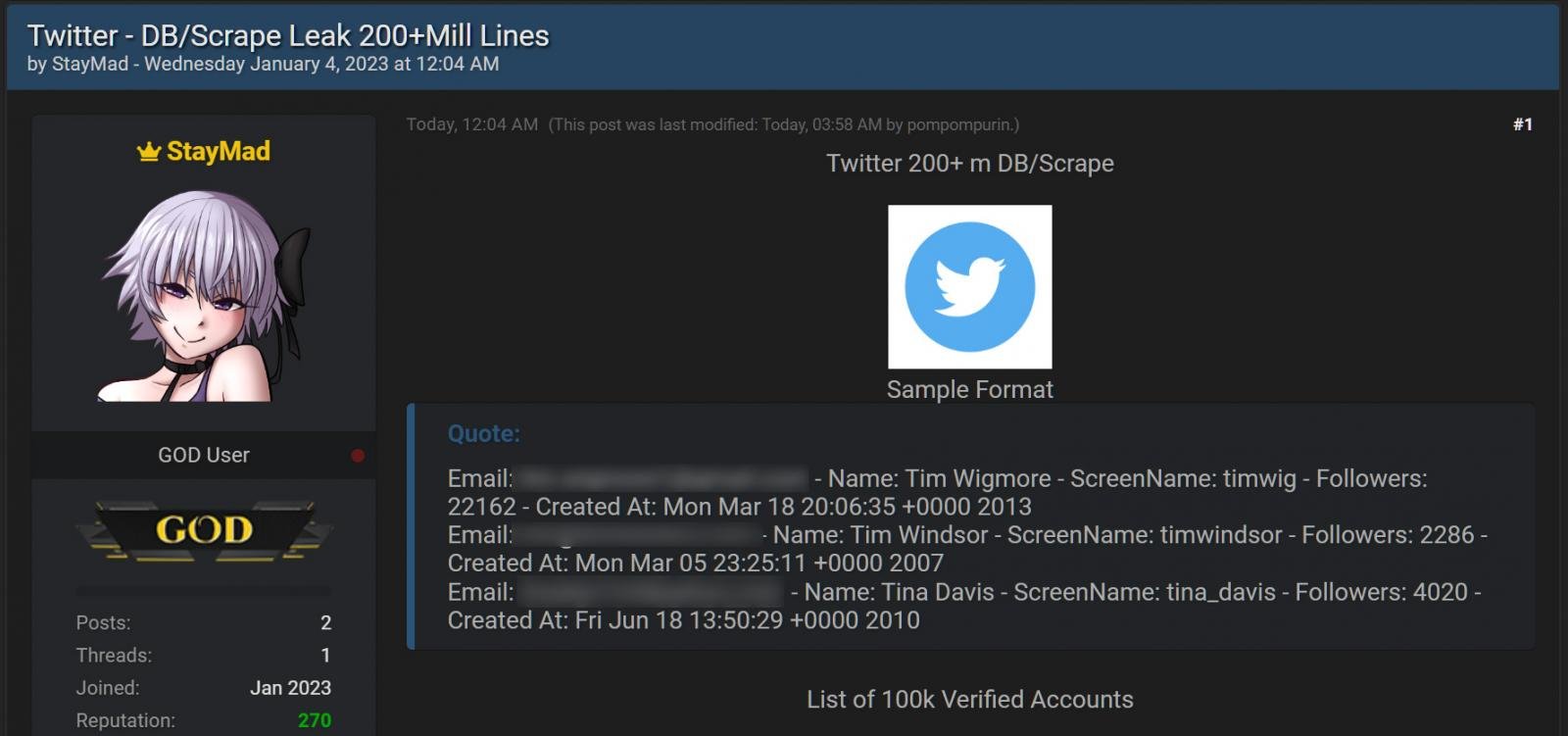
- Twitter’s latest security headache
- Updated on 2023-01-06
- More highlights from the past 24 hours
- Updated on 2023-01-05
- More highlights from the past 24 hours
- Twitter data leak
- Potsdam cyberattack
- 3Commas cyber-heist
- T-Mobile breach settlement
- LastPass gets sued
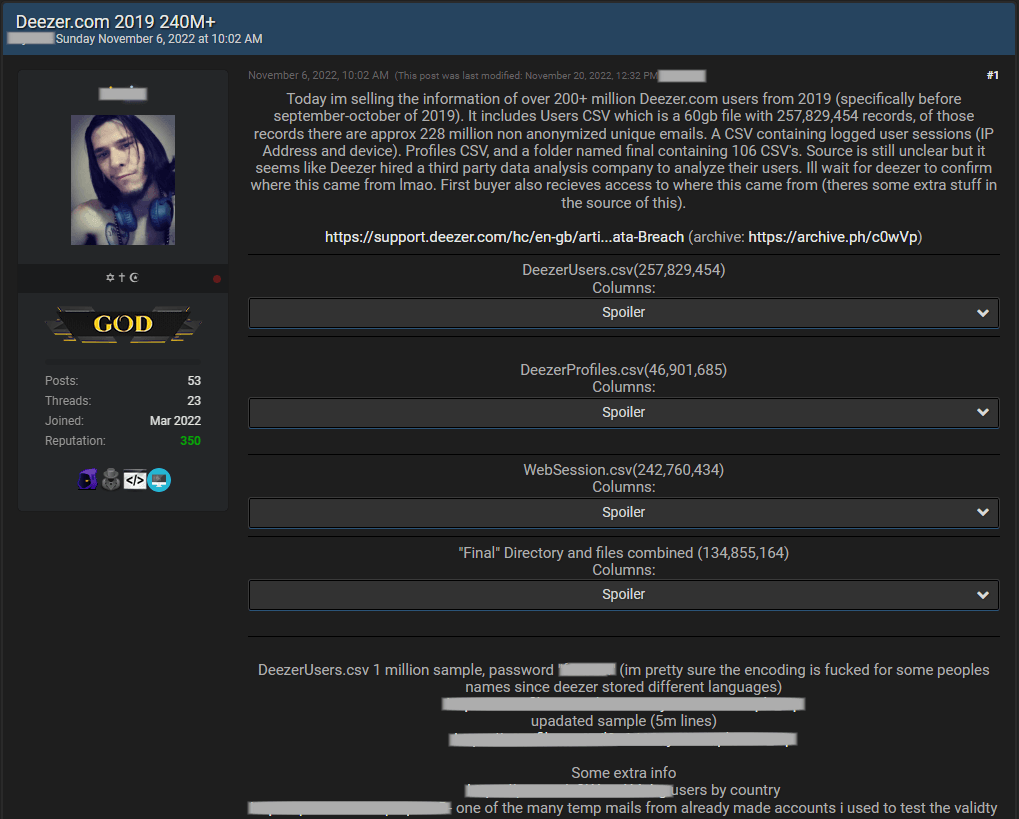
- Deezer data breach
- Five Guys breach
- Meta fined in the EU
- Google spam call warning
- Twitter advertising
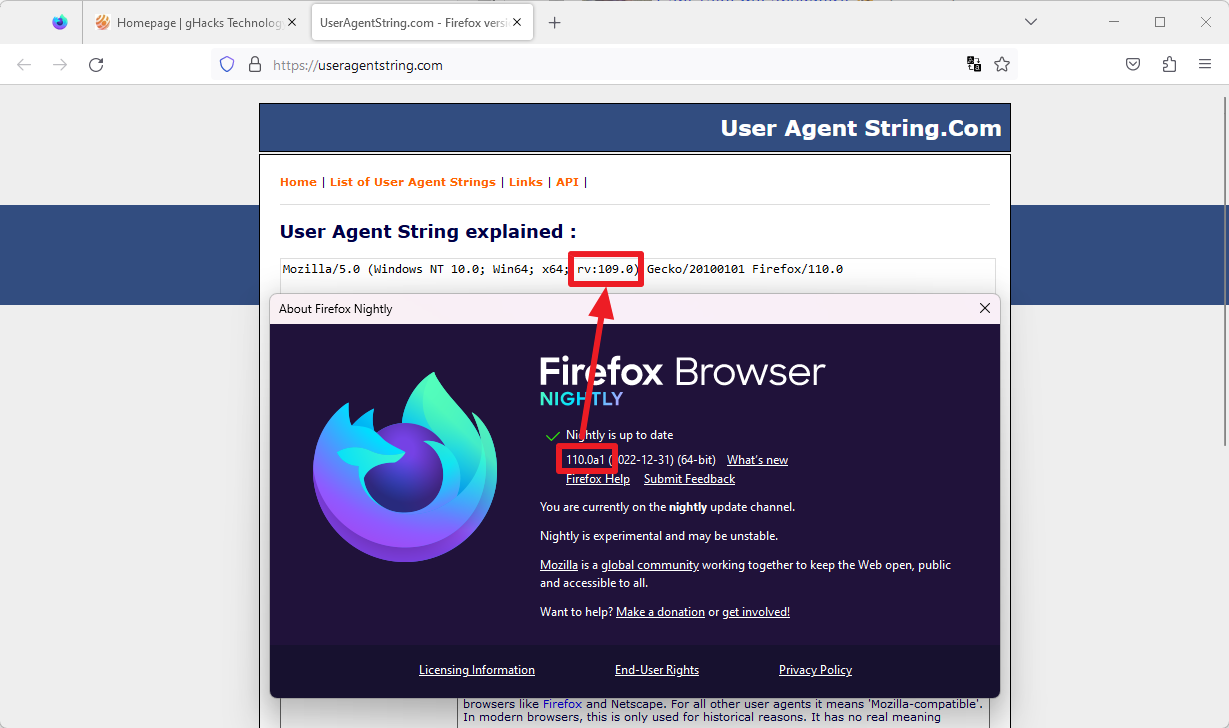
- Firefox browser detection
- Russia’s Android clone
- Ukraine dismantles another bot farm
- Poland warning
- Propaganda pact
- US court ruling on ransomware and insurance
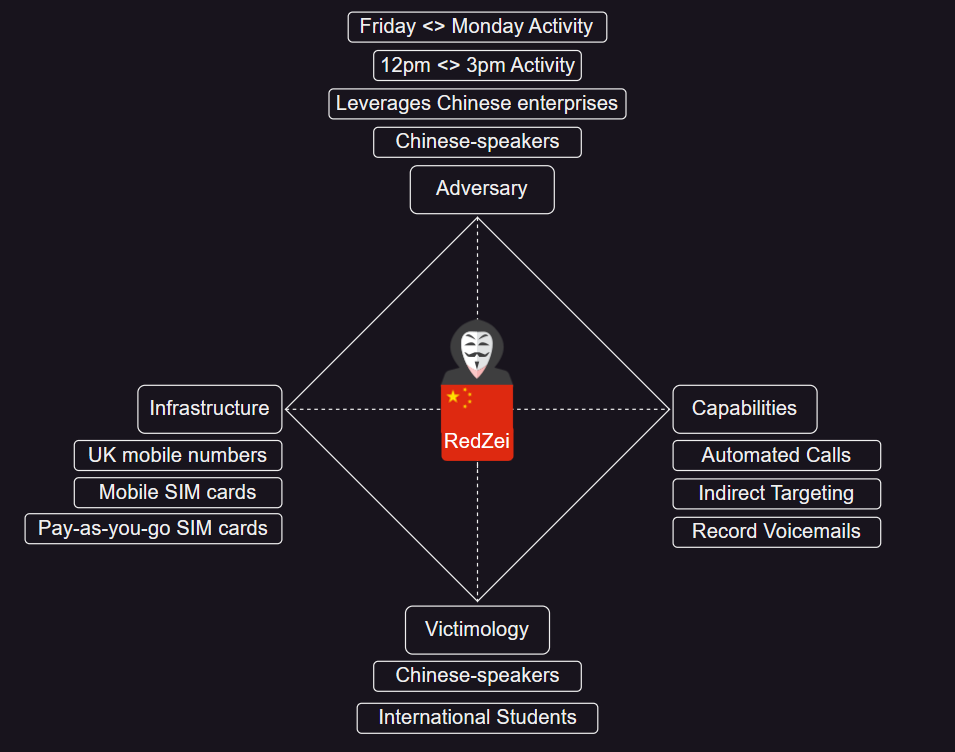
- RedZei
- Data leak site on I2P
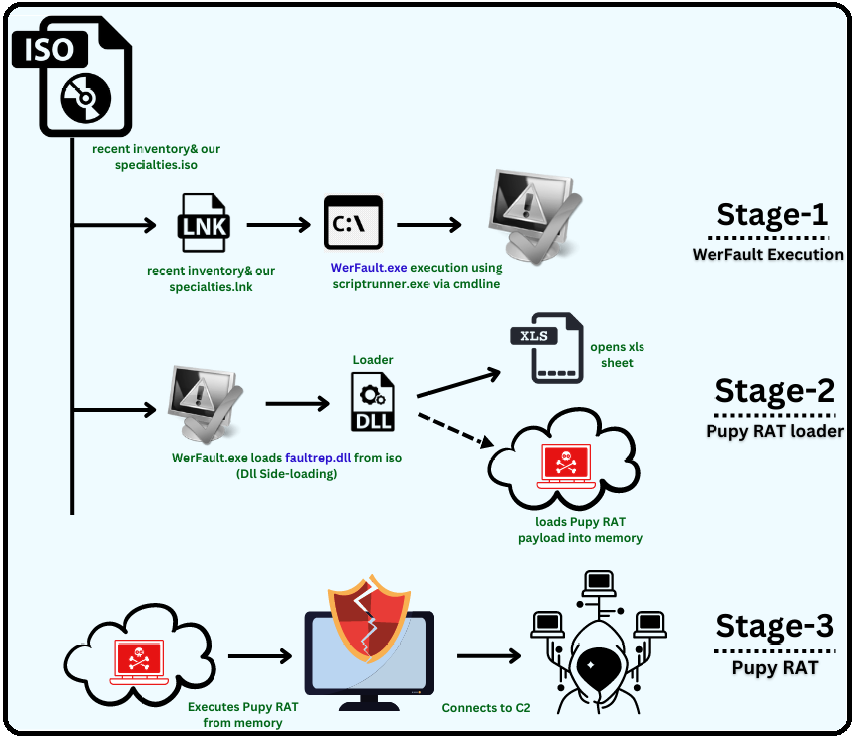
- Pupy RAT campaign
- MBR locker campaign
- New npm malware
- Google Cloud threat analysis
- OrBit dropper
- Hornet ransomware
- CatB ransomware
- Confucious APT
- Transparent Tribe
- Android security updates
- Breaking 2048-bit RSA
- Mastodon DDoS protection
- Google Home smart speaker vulnerability
- ENLBufferPwn
- Twitter whistleblower update
- New tool—dnstwist
- Updated on 2023-01-04
- More highlights from the past 24 hours
- Updated on 2023-01-02
- More highlights from the past 24 hours
Updated on 2023-01-11
SF BART ransomware
The San Francisco Bay Area Rapid Transit (BART) is investigating an intrusion of its IT network after the Vice Society ransomware gang claimed to have compromised the agency via a blog post on their dark web leak site. The agency’s spokesperson told The Record that “no BART services or internal business systems have been impacted,” but they are still looking into claims that data was stolen.
OxShag leak
A dating website named OxShag, which was created by Oxford University students for their fellows, has caused an accidental data leak by exposing everyone’s names and university email addresses. According to The Times, OxShag appears to have listed the university’s entire email directory for both students and administrators alike. The website was shut down following student complaints. Read more: Oxford University dating website for staff and students shut down after ‘huge data breach’

DNV ShipManager attack
Norweigian company DNV says it had to shut down its ShipManager smart ship management platform in the aftermath of a cyberattack that took place last Saturday. DNV said ShipManager would work in offline mode while they investigate the incident together with the Norwegian police. The ShipManager platform, which allows maritime companies to manage ship fleets, their crew, maintenance, procurement, cargo, and other analytics, is currently used by more than 300 maritime companies and installed on more than 7,000 vessels. Read more: Cyber-attack on ShipManager, a DNV software
Cryptome suspension
Twitter has permanently suspended the account of Cryptome.org, a leak site known for publishing leaks of sensitive documents from across the world. The last files published on the site before the suspension are documents claiming to contain Donald and Melania Trump’s tax returns.
Windows 7 end of extended support
As of January 10, 2023, the Microsoft Windows 7 and Windows 8.1 operating systems have formally reached their end of extended support. Both operating systems previously reached their end of life for home users in January 2020, after which point only selected corporate customers were eligible for additional security updates under a commercial plan. These updates will stop this week. Other Microsoft products that also reached their end of support this Tuesday also include Visual Studio 2012 and the Windows RT and Windows Server 2008 operating systems, among many others. Read more: Windows 7 end of support and Office
DDoS attacks on Serbian govt
The Serbian government says it mitigated a two-day-long DDOS attack that hit several of its official websites and IT infrastructure. No group has yet to claim the attacks. Read more: Масoвни сајбер напади на сајт и ИТ инфраструктуру МУП-а
Malta drops Huawei CCTV project
The Maltese government will abandon its joint project with Huawei to implement a facial recognition-based CCTV system across some of its urban areas. Named Safe City Malta, the project was announced in 2018 and was initially deployed in 2019 in two cities—Paceville and Marsa. After years of criticism from privacy advocates, earlier this week, the Maltese government chose not to extend Huawei’s contract and let the project lapse. Read more: Maltese government ditches controversial Huawei ‘Safe City’ CCTV company
DNS4EU
Czech cybersecurity company Whalebone has been selected to build DNS4EU, a public DNS service for the European Union, its agencies, and citizens. Whalebone will lead a consortium of 13 companies based across 10 EU countries. Members include universities, national CERT teams, and other private companies. The project was first announced in January last year. A recording of the press conference and the consortium’s plans is embedded below. Read more: The European Commission plans to onboard 100 million people to a new EU-based DNS internet infrastructure. The DNS4EU will be developed by international consortium led by Czech company Whalebone
US Supreme Court denies NSO Group
The US Supreme Court has declined to hear a petition brought by infamous Israeli spyware vendor NSO Group related to its WhatsApp lawsuit. Meta sued NSO Group in 2019 after the company created and sold an exploit that was used to hack the smartphones of tens of WhatsApp users across the globe. Meta asked a US court for an injunction banning NSO Group from developing future exploits. As part of its legal defense, NSO argued that it was entitled to “sovereign immunity” because the exploit was bought and used by foreign governments that had the authority to use such tools. Lower US courts declined NSO’s petition and request for “sovereign immunity,” and with the Supreme Court ruling the same, the case is now free to move forward. According to the Knight Institute at Columbia University, the decision clears the path for lawsuits by journalists and activists. Read more: Knight Institute Comments on Supreme Court’s Denial of Cert in NSO v. WhatsApp
DOI password audit
The Inspector General at the Office of the Interior carried out a security audit of the password management policies used inside the US Department of the Interior. In a report [PDF] published last week, officials said they were able to crack more than 18,000 of the department’s AD accounts, representing 21% of the department’s entire userbase. Officials said the DOI failed to enforce password complexity requirements, failed to protect 89% of high-value accounts with a form of multi-factor authentication, failed to enforce password age limits, failed to enforce password reuse policies, and also failed to deactivate inactive accounts.
Auction site scammer sentenced
A Romanian national was sentenced to 89 months in prison for his role in a large cybercrime gang that defrauded Americans. The group operated by using stolen identities to create accounts on popular online auction sites, such as eBay, where they posted ads for non-existing goods, and then laundered their ill-gotten funds through cryptocurrency. The man is the fifth member of the gang to plead guilty and receive a long prison sentence. Four other Romanian nationals also previously received prison sentences between 61 and 70 months last year, according to the DOJ. Read more: Man Sentenced for Integral Role in Sophisticated International Fraud Scheme
New npm malware
Fourty-seven new malicious npm packages spotted. Check out GitHub’s security advisory portal for details.
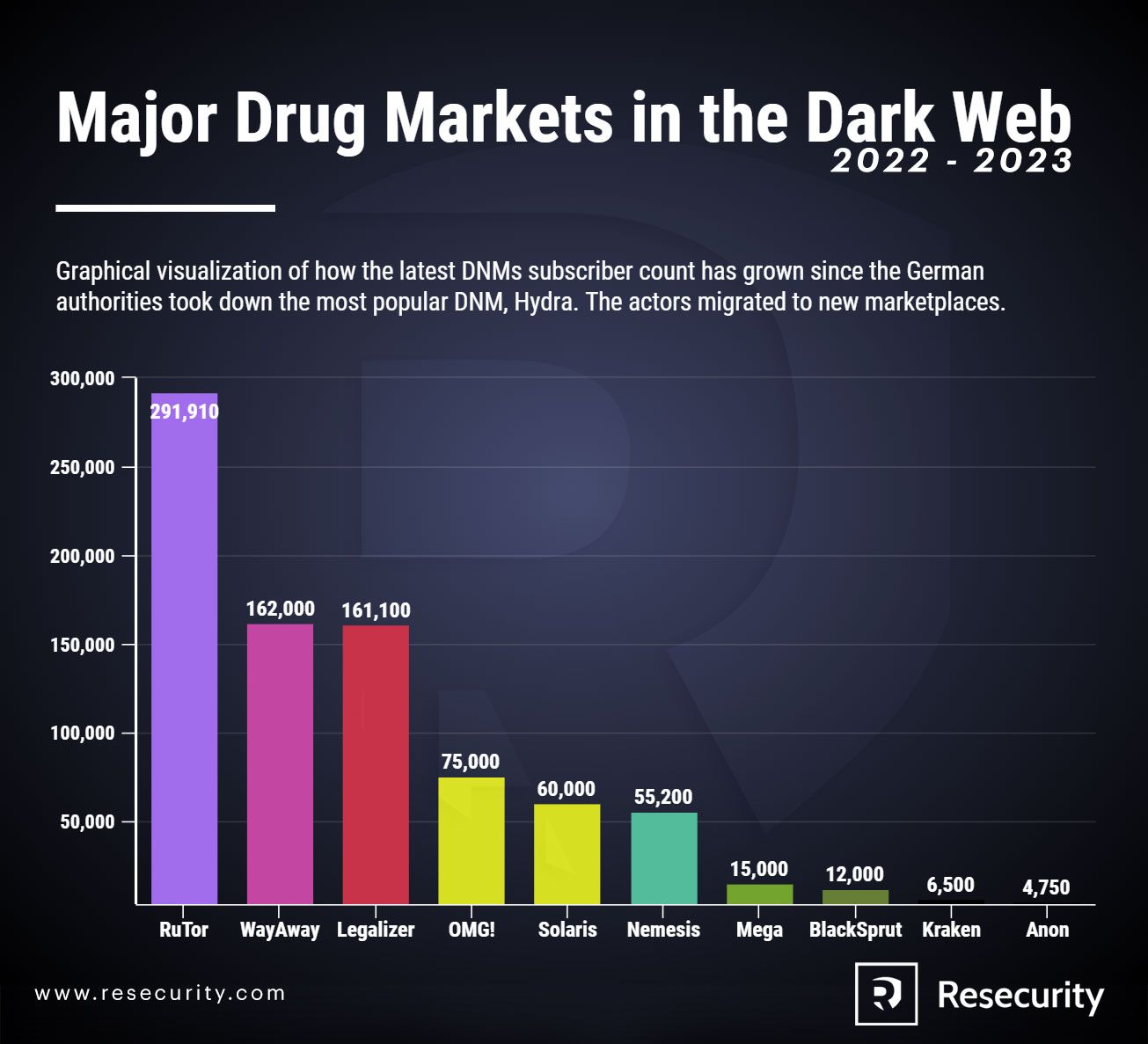
Dark web drug markets
Threat intel company Resecurity says that at least seven dark web marketplaces dedicated to the drug trade have recently released Android apps as a new way for their customers to place orders on their sites. Marketplaces that now run Android apps include the likes of Yakudza, TomFord24, 24Deluxe, PNTS32, Flakka24, 24Cana, and Maps TGK. Read more: Dark Web Markets Compete For The Drug Trafficking And Illegal Pharmacy Monopoly
ScrubCrypt
Perception Point researchers say they discovered a new crypter service named ScrubCrypt. The service is currently being advertised on underground hacking forums and has already been used in the wild to mask the Xworm RAT in recent phishing campaigns. Read more: The Rebranded Crypter: ScrubCrypt
Godfather in Germany
BaFin, Germany’s financial sector regulator, published a public service announcement on Monday warning of attacks carried out with a new strain of malware known as Godfather. First described in a report from Group-IB last year, Godfather is a banking trojan that targets Android devices and which contains functionality to target more than 400 mobile banking and cryptocurrency applications. Read more: Warnung: Aktuelle Schadsoftware „Godfather“ greift Banking- und Krypto-Apps an
Lorenz ransomware update
Security firm S-RM says it is seeing the Lorenz ransomware gang access backdoors planted on Mitel VoIP servers months before in order to launch attacks on companies that failed to detect the initial intrusions. All systems appear to have been compromised via a Mitel zero-day (CVE-2022-29499) that was disclosed last April and which the Lorenz gang is known to have abused in previous months, per reports from Arctic Wolf and Crowdstrike. Read more:
- CYBER INTELLIGENCE BRIEFING SPECIAL: LORENZ OPENS OLD BACKDOORS
- Chiseling In: Lorenz Ransomware Group Cracks MiVoice And Calls Back For Free
- The Call Is Coming from Inside the House: CrowdStrike Identifies Novel Exploit in VOIP Appliance
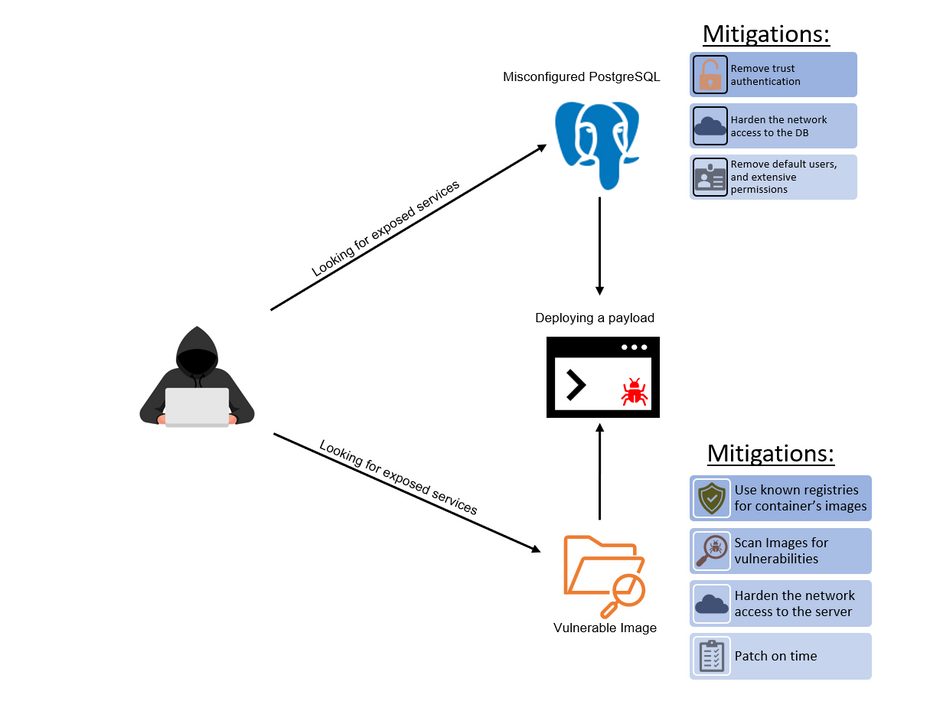
Kinsing attacks
Microsoft has published a report that takes a deep look at the techniques used by the Kinsing cryptomining botnet to breach Kubernetes clusters. According to Microsoft, Kinsing operators preferred two methods. The first targets outdated server images that come pre-packaged with vulnerable applications. The second method targeted Kubernetes clusters that ran misconfigured PostgreSQL databases.
URSNIF
The fantastic team at the DFIR Report has published a new report that goes into the finer details of a URSNIF attack. The intrusion started with an ISO file and ended six days later after the attackers extracted access credentials from the company’s network. According to the DFIR Report team, “the threat actor was able to RDP to a backup server using the admin credentials they acquired.” Read more: Unwrapping Ursnifs Gifts
Raspberry Robin partial takedown
Cybersecurity firm Sekoia says the Raspberry Robin lost 80 (30%) of its command and control (C&C) servers in October last year as part of a partial takedown operation. The company’s report takes a look at how the botnet’s operators reacted after losing a large chunk of their servers. Read more: Raspberry Robin’s botnet second life
“These domains had their DNS zone deleted and the tags clientHold, clientTransferProhibited were added to their status codes, leading to a total loss by the botnet operators.”
PlugX analysis
Malware researcher Tìm Kiếm has published a technical analysis of a recently discovered PlugX malware sample. The malware is typically used by Chinese APTs, but Kiếm makes no formal attribution. Read more: [QuickNote] Another nice PlugX sample
Hive’s XDR33 variant
Netlab, the network security division of Chinese security firm Qihoo 360, says it discovered a new malware strain named XDR33 that appears to be a new variation of Hive, a malware control framework supposedly developed by the CIA.
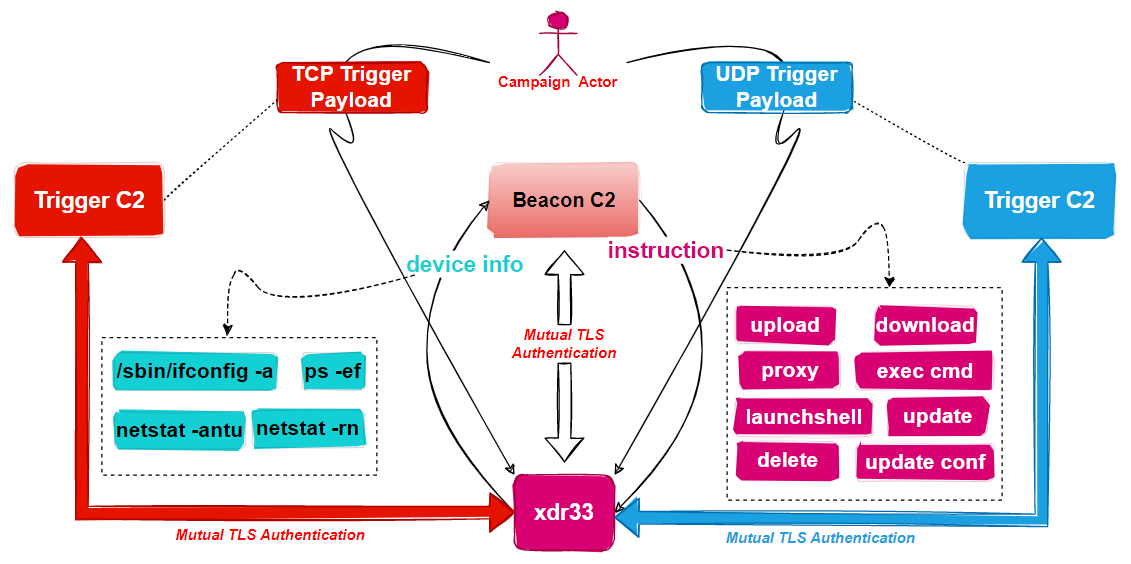
Hive is one of the tools that had its documentation leaked by WikiLeaks in 2017 as part of the Vault7 collection. Netlab researchers said they discovered the XDR33 variant last year in October being deployed on F5 devices, where the malware would act as a backdoor. Netlab says this is the first time they found a variant of the CIA Hive malware kit in the wild. Netlab didn’t attribute XDR33 and the recent attacks to the CIA, at least, not yet. The report comes after China’s CERT agency issued an alert in April last year about attacks carried out with the CIA’s Hive malware—attacks which they directly attributed to the CIA. Read more:
- Heads up! Xdr33, A Variant Of CIA’s HIVE Attack Kit Emerges
- Vault 7: CIA Hacking Tools Revealed
- Exclusive: How CIA uses cyber weapon ‘Beehive’ to monitor, attack global key targets
StrongPity APT
ESET researchers have uncovered a new operation carried out by the StrongPity APT where the group created a website that impersonated Shagle, a video chat service that lets users have encrypted video chats with random strangers. ESET says StrongPity’s goal was to get users to download and install an Android app that was a modified version of the open-source Telegram app, repackaged with one of the group’s backdoors.
Threema vulnerabilities
A team of academics from the ETH Zurich University has published a technical paper on a series of vulnerabilities in Threema, a secure end-to-end encrypted messaging service that bills itself as a Signal and WhatsApp alternative. The seven vulnerabilities can allow a threat actor to impersonate a user, gain access to Threema servers, and gain access to Threema data on an unlocked device. Responding to the research, Threema said the vulnerabilities impact an older version of its protocol “that is no longer in use.” The company’s response turned out to be both dismissive and misleading and the research team said their work is what forced the company to update to its curent and a newer protocol.
$1 million bounty
A security researcher was awarded a $1 million bug bounty reward after discovering and reporting a vulnerability that impacted three parachains running on the Polkadot blockchain, namely the Moonbeam, Astar Network, and Acala projects. According to cryptocurrency news outlet The Block, the researcher said that if the vulnerability had been exploited in the wild, an attacker could have stolen as much as $200 million worth of crypto-assets from the three projects.
Experian website bug
Credit reporting agency Experian has patched a bug in its website that allowed identity thieves to view credit reports and the personal details of any of the company’s customers. The bug was super simple to exploit and consisted of replacing a part of the Experian website URL in the security questions page (/acr/oow/ with /acr/report/). According to KrebsOnSecurity, the issue was discovered last year by a Ukrainian security researcher who saw it mentioned on Telegram channels dedicated to online fraud.
Taking over a dead IoT company
Security researcher Kevin Chung has taken over an old domain used by NYCTrainSign, a now-defunct company that sold displays that show the time until a certain NYC train would hit a certain train station. Chung also wrote an exploit that allowed him to get full control of any signs still in the field.
CVE-2022-23529
Palo Alto Networks researchers have discovered a vulnerability in the JsonWebToken open-source project that can be used to achieve remote code execution (RCE) on a server verifying a maliciously crafted JSON web token (JWT) request.
CVE-2022-43974
Deutsche Telekom security researcher Alissar Ibrahim has published details [PDF] about a critical buffer overflow vulnerability in the MatrixSSL library. Ibrahim says the issue can allow an attacker to overwrite a large part of a server’s RAM and lead to remote code execution. The issue was fixed with the release of MatrixSSL 4.6.0 last month.
Asus router vulnerabilities
Asus has patched a set of three vulnerabilities that can be used to bypass authentication in some of its newer router models and take over devices. Details are available via Cisco Talos.
Siemens PLC vulnerabilities
Red Balloon researchers have discovered a series of vulnerabilities in the firmware of Siemens SIMATIC and SIPLUS S7-1500 Series PLC devices, commonly deployed in industrial networks. Researchers say the vulnerabilities can allow attackers to bypass all protected boot features, resulting in persistent arbitrary modification of operating code and data on vulnerable PLCs. Red Balloon described the issues as “architectural vulnerabilities,” meaning they can’t be patched at a software level. Siemens has published recommendations for its users regarding workarounds and mitigations [PDF].
Patch Tuesday
Yesterday was also this year’s first Patch Tuesday. We had security updates being released by Adobe, Microsoft, and SAP. Zoom, Lenovo, and the Android project released security updates last week as well. This month, Microsoft patched 98 vulnerabilities, including an actively exploited zero-day (CVE-2023-21674). On the same topic, vulnerability management company Tenable also published a blog post delving into the history and evolution of Microsoft Patch Tuesday security updates over the past few years.
New tool—ImageMagick Security Policy Scanner
DoyenSec has open-sourced the code of a new web-based tool named ImageMagick Security Policy Scanner, which, as it name implies, can scan and detect misconfigurations in ImageMagick library configs.
New tool—cobalt-strike-stager-parser
Security firm Stairwell has open-sourced this week a new tool that can decode Cobalt Strike staging shellcode.
Red Hat Insights
Red Hat has formally launched Red Hat Insights, a malware detection service for RHEL systems.
Updated on 2023-01-10
A recent data breach at a third-party vendor for gastroenterologists has affected almost a quarter million patients who underwent a colonoscopy since 2019, adding to the already invasive nature of the procedure. In another vein, a restaurant chain acknowledged that hackers abused some of its customer accounts. Moving on to phishing, a new campaign is leveraging Facebook copyright notices to extract credentials. Read along to know what transpired in the past 24 hours.
More highlights from the past 24 hours
Kansas-based Captify Health is notifying 244,300 patients that their personal data and payment card details, dating back to 2019, were potentially compromised in a data breach. Read more: Data Breach Notifications
Chick-fil-A warned customers about suspicious activity on their accounts. Investigation is ongoing and no compromise of internal systems has been detected – stated the restaurant chain.
San Francisco’s Bay Area Rapid Transit (BART) is investigating an alleged ransomware attack after the Vice Society ransomware gang claimed to have breached the agency.
The Serbian government announced that the IT infrastructure and website of its Ministry of Internal Affairs were hit by a wave of DDoS attacks. Read more: Масoвни сајбер напади на сајт и ИТ инфраструктуру МУП-а
Attackers exploited an open redirect official website of the U.K DEFRA to direct targets to fake OnlyFans adult dating sites, with an aim of stealing their personal information. Read more: UK gov website being used to redirect to porn sites
Avanon researchers spotted a new credential harvesting campaign that is leveraging Facebook copyright infringement notices to pilfer credentials from unsuspecting users. Read more: Facebook Termination Notices Leads to Phishing
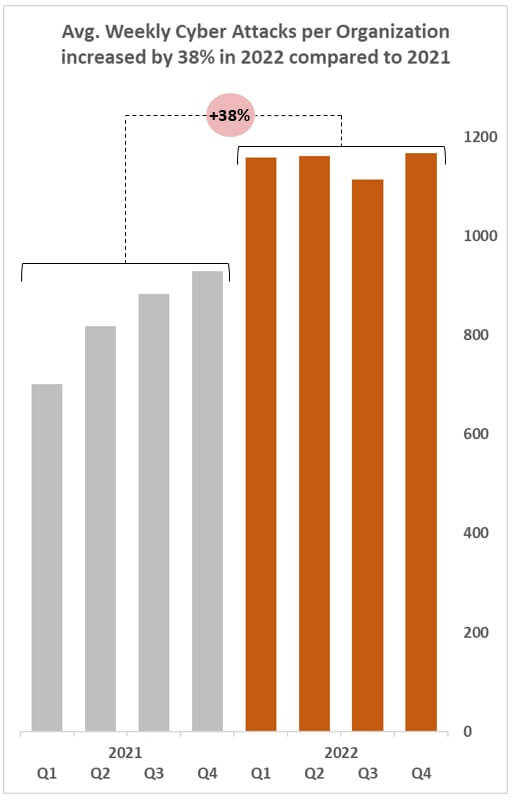
New research by Check Point revealed that the number of cyberattacks in 2022 rose by 38%, as compared to 2021. Also, Q4 2022 observed the highest number of attacks at 1,168 weekly attacks per organization. Read more: Check Point Research Reports a 38% Increase in 2022 Global Cyberattacks
Resecurity reported that dark web markets selling drugs and other illegal substances have resorted to custom Android apps to evade law enforcement and strengthen privacy. Read more: Dark Web Markets Compete For The Drug Trafficking And Illegal Pharmacy Monopoly
Microsoft observed a new Kinsing cryptojacking operation that is abusing misconfigured and exposed PostgreSQL servers to gain initial access to Kubernetes environments. Read more: Initial access techniques in Kubernetes environments used by Kinsing malware
Greek cybersecurity training startup Hack the Box raised $55 million from Carlyle Group. The company aims to invest the amount in research and development. Read more: Αμερικανικό fund επενδύει στην ελληνική Hack The Box
Updated on 2023-01-09
Russian hackers have been incessantly targeting Ukrainian allies since the invasion last year. In one such incident, researchers revealed that a Russian threat actor targeted three U.S. nuclear laboratories in 2022. If you’re a Flying Blue customer, your data might have been compromised in a breach on KLM and Air France. In other news, a data breach at a Texas municipal ambulance service provider affected hundreds of thousands of people. Here is everything that happened in cyberspace over the weekend.
More highlights from the past 24 hours
Reuters revealed that the Russian hacking group, named Callisto (Cold River), had targeted the Argonne, Brookhaven, and Lawrence Livermore National Laboratories between August and September 2022. Read more: Exclusive: Russian hackers targeted U.S. nuclear scientists
Air France and KLM started notifying their Flying Blue loyalty program customers that some of their personal information, including earned miles balance, was compromised in a breach.
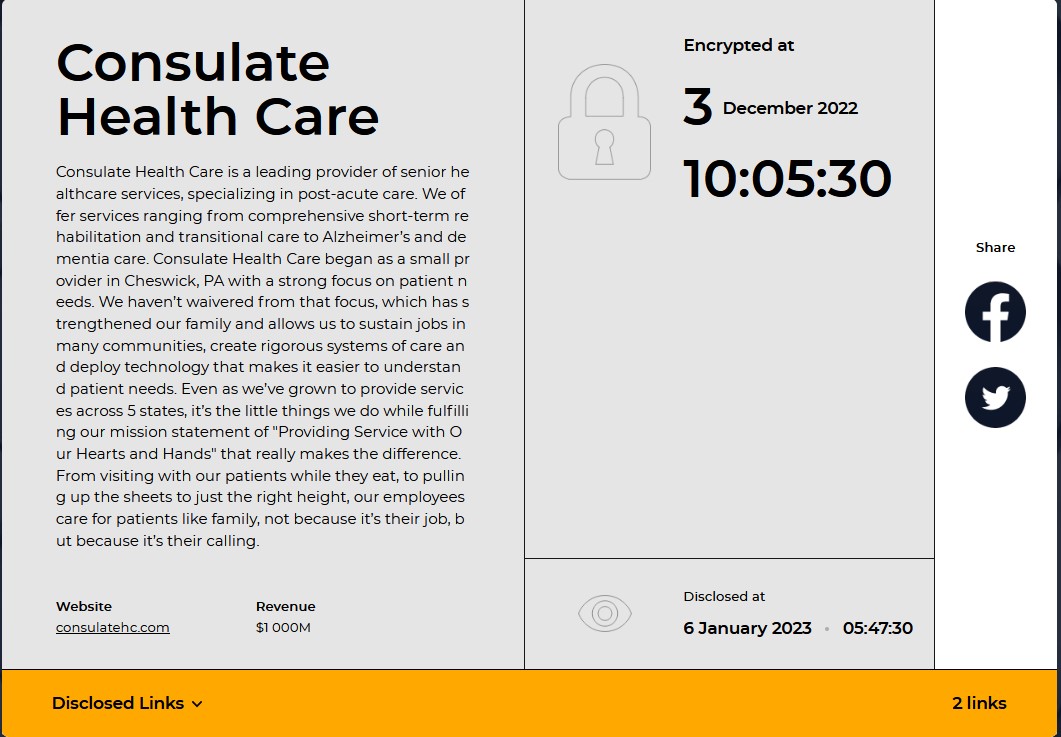
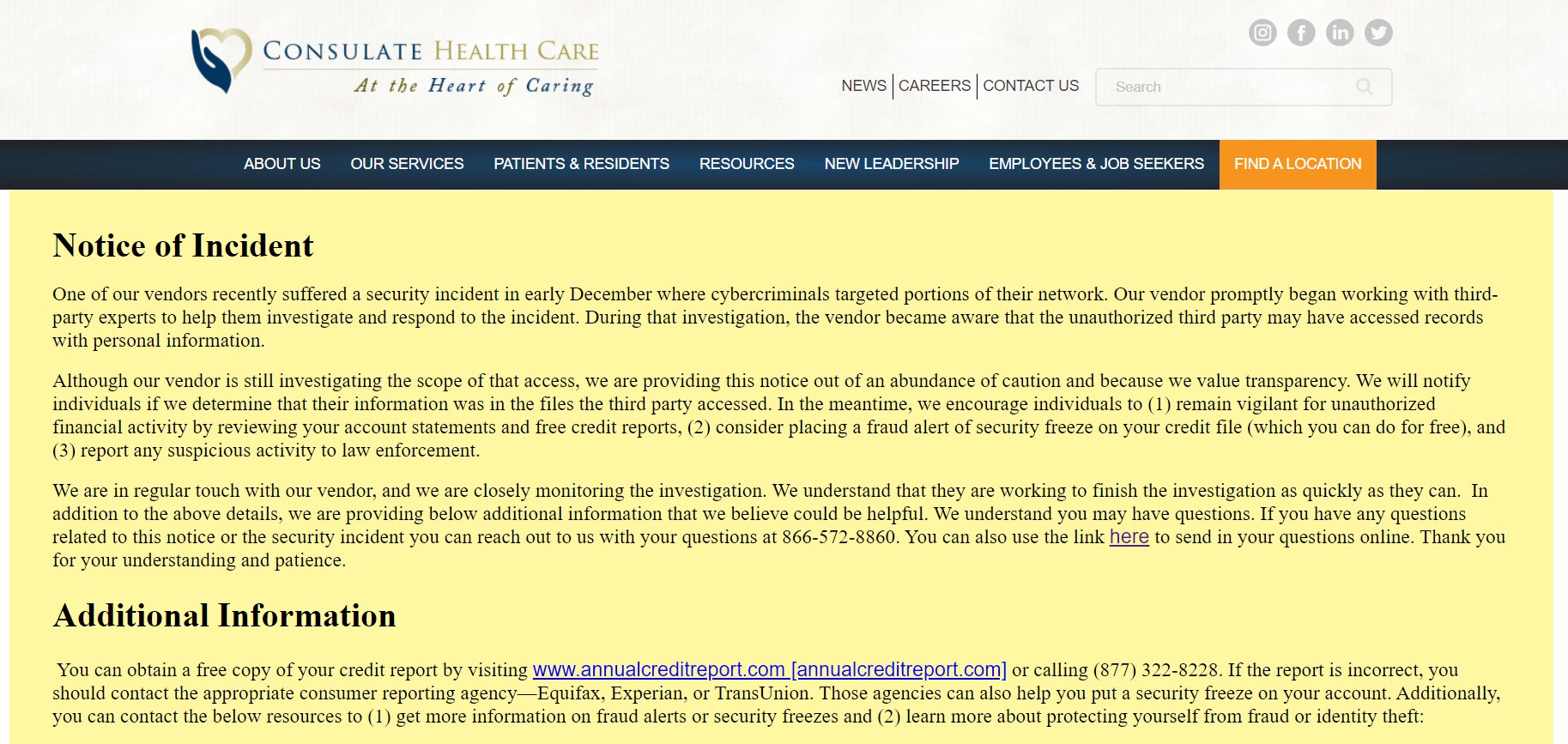
The Hive ransomware group leaked 550 GB of data, including employee and customer PII, stolen from Consulate Health Care. While the attack was disclosed on January 06, the attackers claim it occurred on December 03, 2022.
Pennsylvania-based Maternal and Family Health Services revealed a ransomware attack from April 2022, which compromised patient medical and financial data. Read more: Important Information about Maternal & Family Health Services’ 2022 Cybersecurity Incident
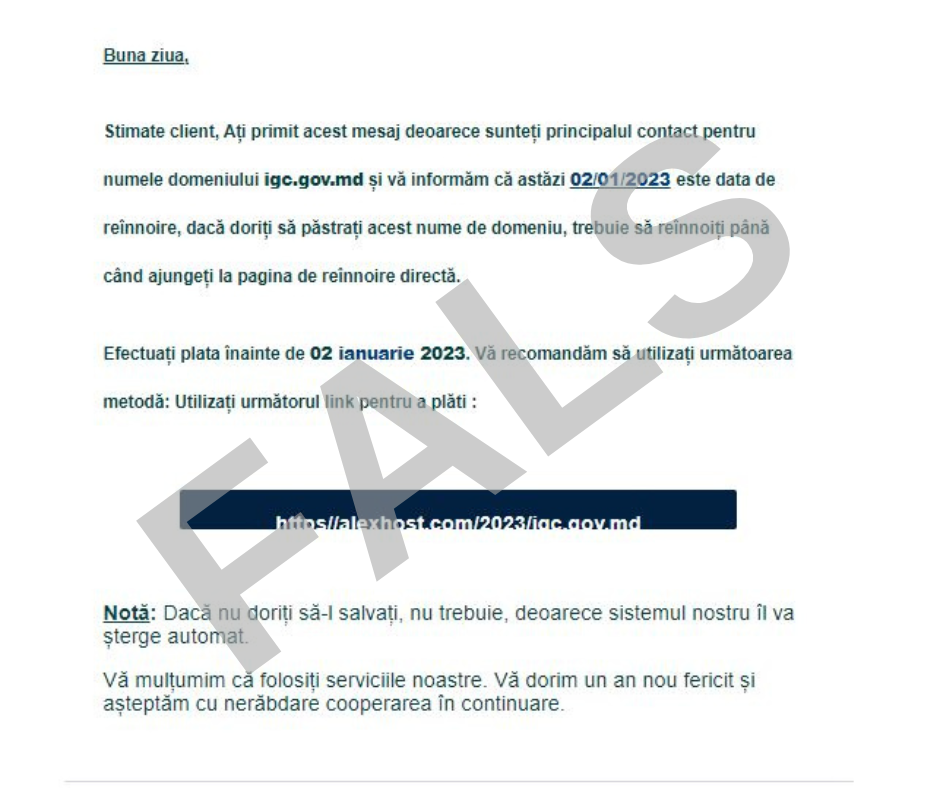
Moldova’s government was the victim of a wave of phishing attacks, in which hackers sent over 1,330 emails to the nation’s state services. The phishing emails were purportedly sent by the website hosting company Alexhost. Read more: STISC: ATENȚIE – continuă valul atacurilor cibernetice de tip scam și phishing
Hackers are using a carefully designed Pokemon NFT card game website to deliver the NetSupport remote access tool and take control over victims’ devices. Read more: Distribution of NetSupport RAT Malware Disguised as a Pokemon Game

A new Dridex malware strain was found targeting devices running macOS. It is delivering documents embedded with malicious macros via a Mach-O executable file.
Phylum spotted an attack campaign—between December 22 and December 31, 2022—targeting the PyPI repository. It used six malicious packages to propagate info-stealers on developers’ systems. Read more: A Deep Dive Into poweRAT: a Newly Discovered Stealer/RAT Combo Polluting PyPI
Cyble researchers warned of a phishing campaign targeting Zoom users to deploy the IcedID trojan. The phishing website mimics the legitimate Zoom website.
Updated on 2023-01-08
Chick-fil-A security incident
Fast-food restaurant chain Chick-fil-A says it’s investigating suspicious activity on a number of customer accounts. The incident appears to be a generic credential stuffing attack that typically targets companies that run loyalty and reward-points programs. These accounts are often hacked and then sold on underground forums. Buyers purchase these accounts and then use the loyalty points to place orders in their name. Several Chick-fil-A users reported on social media having their accounts hacked and emptied of loyalty points in recent weeks, which most likely triggered the company’s investigation. Read more: Customer Support > Chick-fil-A One Membership Program > Suspicious Activity
AirFrance-KLM incident
French-Dutch airline company Air France–KLM notified customers last week of a security breach that impacted the account owners of its FlyingBlue loyalty program. In an email sent to affected customers, the company says details such as names, phone numbers, email addresses, and latest transactions were exposed in the incident.
Ray-Ban lawsuit
A US judge has ruled that JPMorgan Chase must face a lawsuit from EssilorLuxottica, the company behind Ray-Ban glasses, after the bank failed to detect and stop suspicious transactions that originated from the eyewear company’s New York bank account. EssilorLuxottica lost $272 million in 2019 after hackers recruited one of the company’s Thai employees, which then made several rogue transactions to a third-party account. In its lawsuit, EssilorLuxottica claimed that JPMorgan should have detected the sudden spike in its regular monthly transfers jumping from $15 million to $100 million. Read more: Ray-Ban manufacturer sues JPMorgan over $272 million cyber theft
WhatsApp gets proxy support
Meta has announced support for proxy connections in its WhatsApp service. The company says the new feature will prove useful for users who want to bypass censorship in oppressive regimes. Besides that, it can also be used to bypass firewalls in corporate environments too. Read more: Connecting to WhatsApp by Proxy
Apple fined in France
CNIL, France’s privacy watchdog, has fined Apple €8 million for showing targeted ads to French users. The agency says that Apple did not obtain explicit consent from users to have their data harvested and used for targeted ads, a clear violation of the EU’s GDPR rules. Read more: Advertising ID: APPLE DISTRIBUTION INTERNATIONAL fined 8 million euros
Louisiana porn law
A new law has entered into effect in the US state of Louisiana where any website where more than a third of its content is adult-related must perform age verification of its visitors. This has led to some websites, such as PornHub, requiring Louisiana residents to verify themselves using a government-issued ID, such as a driver’s license. Read more:
- Watching porn now requires age verification in La. because of new law
- You Now Need a Government ID to Access Pornhub in Louisiana
DDoS attack on Danish Army
Pro-Russian hacktivists carried out DDoS attacks on the websites of the Danish Army last month. Exemplifying just how unimportant and unimpactful these attacks really are, it took Danish officials four hours to spot the attacks (because nobody actually cares if you DDoS a generic website) and another 11 hours to block them. Read more: Det tog 11 timer for Forsvaret at afværge cyberangreb på hjemmesider
Cyber-attacks on Moldova
STISC, Moldova’s cybersecurity agency, has put out a warning about a massive phishing campaign that is currently targeting owners of Moldovan .md web domains with an “expired domain” lure. The campaign got the agency’s attention after the attackers spammed more than 1,300 government email inboxes that were being used to manage official government websites.
Wikipedia’s Saudi Arabia scandal
Reports from two human rights organizations and The Guardian claim that the Saudi Arabian government infiltrated the Wikipedia editorial staff as part of a concerted effort to control the site’s content. These admins supposedly promoted positive content about the government and deleted critical items, such as information about human rights abuses and political prisoners. The Saudi agents also allegedly helped identify at least two Saudi citizens who edited the site with critical content, individuals who were later detained and sentenced to heavy prison sentences. The reports come after Wikipedia banned 16 users in its MENA region last month. The two NGOs criticized Wikipedia for its generic announcement and for not revealing any kind of details about the incident, which contrasts with the high level of transparency the organization showcased in past cases. In a statement last week, after the case got media attention, Wikipedia again refused to disclose details about the ban, said the reports contained “many material inaccuracies,” and played dumb by claiming they don’t know “where these volunteers actually reside.” Read more:
- Saudi Arabia: Government Agents Infiltrate Wikipedia, Sentence Independent Wikipedia Administrators to Prison
- Saudi Arabia jails two Wikipedia staff in ‘bid to control content’
Rogue Dutch govt employee
Dutch prosecutors are seeking a three-year prison sentence for a former employee of the Dutch Tax and Administration service. Investigators say the suspect used his access to government systems to search sensitive information for cash. Officials say the suspect searched and shared information for license plate numbers, social security numbers, home addresses, if an individual had kids, or where the individual’s parents lived. The suspect allegedly charged €10,000 per search, and authorities seized €920,000 from their Amsterdam home following their arrest. Read more: Eis: drie jaar cel tegen medewerker Belastingsdienst
Ransomware investigation
Florida prosecutors are investigating if a former school superintendent and two other former IT administrators broke the law when they used undisclosed details from a March 2021 ransomware attack against the Broward school district, their former employer, as part of their business sales pitches. Read more: Broward school district asks for external review on data breach concerns
NSO update
The management of five companies linked to NSO activities has recently moved from Luxembourg to London, UK. Read more: Management of five firms linked to Pegasus maker NSO is moved to London
C&C server list
Security researcher Rohit Bansal has published a list of 82 command and control servers for the Rhadamanthys infostealer.
eBPF malware usage
Security firm Red Canary has a breakdown of how the eBPF (extended Berkeley Packet Filter) networking utility is being used by Linux malware strains. Read more: eBPF: A new frontier for malware
Mac ransomware
Microsoft (out of all people) has a breakdown of the most common techniques used by Mac ransomware.
Mac malware of 2022
More than half of the 13 new macOS malware strains discovered last year are believed to be the work of Chinese state-sponsored hacking crews. According to macOS malware researchers Patrick Wardle, this includes strains such as the Rshell backdoor, the Alchimist malware framework, the DazzleSpy spyware, the oRAT trojan, and the SysJoker backdoor. Read more: The Mac Malware of 2022 [PDF]
New ransomware
Fortinet has a report on new ransomware families that have been spotted in the wild over the past few weeks. This includes the like of Monti, BlackHunt, and Putin (not that Putin). Read more: Ransomware Roundup – Monti, BlackHunt, and Putin Ransomware
Automated Libra’s PurpleUrchin
Palo Alto Networks says they’ve spotted a threat actor named Automated Libra engage in freejacking, a type of attack against cloud hosting companies where threat actors sign up for accounts in order to host cryptomining apps on high-power cloud servers. Palo Alto Networks says the group employed a “play and run” tactic where they registered accounts using stolen identities and then disappeared when the cloud vendor’s bills came due. Researchers say this campaign, which they named PurpleUrchin, began in November 2022 and involved more than 130,000 automatically-registered accounts on services such as Heroku, Togglebox, GitHub, and others. Read more: PurpleUrchin Bypasses CAPTCHA and Steals Cloud Platform Resources
Dridex update
Trend Micro researchers say they spotted a version of the Dridex malware that was designed to target macOS systems. The sample was first spotted in the wild in 2019 but was never effective, as its final payload was a Windows executable that would crash on macOS systems. Trend Micro warns that despite this, the malware is one update away from being fully macOS-compatible.
poweRAT
DevSecOps security firm has published a report on poweRAT, a new remote access trojan that was distributed via malicious Python libraries uploaded on the official PyPI portal at the end of last year. Six malicious libraries were found to contain the malware, and what stood out about this threat was its use of the Cloudflare Tunnel tunneling service to bypass local firewalls and exfiltrate stolen information (such as browser data and stored secret tokens/keys). Read more: A Deep Dive Into poweRAT: a Newly Discovered Stealer/RAT Combo Polluting PyPI
BlueBottle
Broadcom’s Symantec security team has a technical report on the techniques used by the BlueBottle threat actor. This is the same threat actor known as OPERA1ER, responsible for the theft of more than $11 million from banks in French-speaking countries across Africa. Read more: Bluebottle: Campaign Hits Banks in French-speaking Countries in Africa
SpyNote leak
ThreatFabric researchers say they’ve recorded a spike in detections for the SpyNote (SpyMax) Android trojan in the last quarter of 2022. Researchers linked the sudden spike in detections to CypherRAT, a custom-made version of SpyNote that had been sold via a Telegram channel since the summer of 2021. ThreatFabric says CypherRAT’s author decided to abandon the project to work on a new Android remote access trojan named CraxsRat, and uploaded the CypherRAT source code on GitHub in October last year before making the switch. Read more: SpyNote: Spyware with RAT capabilities targeting Financial Institutions
BlindEagle APT
CheckPoint has a report out on Blind Eagle (APT-C-36), a dual financial and cyber-espionage APT group that has targeted various countries across South America since 2018. The report covers the group’s most recent operations that have targeted organizations in Ecuador. Read more: BLINDEAGLE TARGETING ECUADOR WITH SHARPENED TOOLS
Rattlesnake APT
Chinese security researchers have put out a report on Rattlesnake, an Indian APT also known as SideWinder, and a recent operation that took place in November 2022 and targeted Chinese universities. Read more: 响尾蛇组织窃密木马通信分析
Saaiwc Group
Researchers with the Anheng Information Hunting Lab have published a report detailing the activities of a new APT they named Saaiwc Group. This campaign targeted military and financial departments in the Philippines, Cambodia, and Vietnam. Read more: 东南亚地区的新晋势力:新APT组织Saaiwc Group针对东南亚军事、财政等多部门的攻击活动分析
Kimsuky APT
Antiy’s security team has a report out on attacks carried out by the Kimsuky North Korean APT group against South Korean organizations. The report focuses on the group’s Android malware arsenal, specifically on malware known as FastFire, FastViewer, and FastSpy—previously covered in an S2W Talon report. Read more:
- Kimsuky移动端恶意活动瞄向韩国东亚研究所国家安全主任
- Unveil the evolution of Kimsuky targeting Android devices with newly discovered mobile malware
Cold River APT
Reuters reports that Russian cyber-espionage group Cold River (aka Callisto) has targeted three nuclear research laboratories in the United States between August and September last year, just as Russian officials were escalating their nuclear threats. Targeted entities included the Brookhaven, Argonne, and Lawrence Livermore National Laboratories. Reuters also says the group made multiple OpSec mistakes in recent years, which allowed security researchers to identify one of its members as Andrey Korinets, a 35-year-old IT worker and bodybuilder from the Russian city of Syktyvkar.
Turla APT
In a report published last week, Mandiant says that Russian cyber-espionage group Turla has hijacked the command and control (C&C) servers of an old Andromeda botnet in order to sift through its compromised hosts and cherry-pick systems of an intelligence and espionage value. Mandiant says that while the botnet had been live since 2013 and had infected systems all over the world, they only observed Turla deploying their custom malware to systems based in Ukraine. Previous reporting has linked Turla with Russia’s FSB intelligence agency. The targeting of Ukrainian-only systems through the Andromeda botnet hijack fits into the FSB’s supporting role in Russia’s invasion of Ukraine. Mandiant says Turla hijacked the botnet by registering a C&C domain that had expired in previous years. Read more: Turla: A Galaxy of Opportunity
ReDoS beg bounties
Trail of Bits researcher William Woodruff argues in a blog post last year that companies would be better off if they ban reports for ReDoS (regular expression denial of service) vulnerabilities in their bug bounty programs as “signal-to-noise ratio on ReDoS reports is unacceptable.” Read more: ReDoS “vulnerabilities” and misaligned incentives
AWS keys on PyPI
Security researcher Tom Forbes says he scanned every package on the PyPI portal and found 57 AWS access keys that were still valid. Some of these keys belonged to entities such as Amazon itself, the Australian government, Intel, and analytics company Terradata. Read more: I scanned every package on PyPi and found 57 live AWS keys
OWASSRF, TabShell
Viettel Cybersecurity researchers have published details about two vulnerabilities they discovered in Microsoft Exchange servers. The vulnerabilities are publicly known as OWASSRF (CVE-2022-41080) and TabShell (CVE-2022-41076), and the former has already been exploited in the wild. Read more: The OWASSRF + TabShell exploit chain
CVE-2022-43931
Patch your Synology VPN servers. This one is a 10/10 RCE, just the stuff threat actors like. Read more: Synology-SA-22:26 VPN Plus Server
CVE-2022-47523
Also, patch your Zoho ManageEngine gear for this SQLi bug. Read more: SQL Injection Vulnerability – CVE-2022-47523
CVE-2022-39947
Also-also, patch your Fortinet ADCs while you’re at it too. There’s a nasty OS command injection vulnerability, but, probably not that bad as it’s a post-auth issue only.
New tool—Hardeneks
Amazon’s AWS division has open-sourced a tool named Hardeneks that can scan AWS Elastic Kubernetes Service (EKS) instances and see if servers follow recommended best practices.
Updated on 2023-01-07
Rackspace blames zero-day for ransomware hit
Rackspace customers finally got a sense of the cyberattack that hosed the company’s hosted Exchange email environment following a ransomware attack in December. Rackspace said in an update this week that some 27 customers had their Exchange backups (.PST files) accessed in the attack, which was caused by an Exchange zero-day, it said, adding that Microsoft hadn’t disclosed the bug was remotely executable. The company also said the attack was caused by the Play ransomware group, which Crowdstrike warned about some weeks back. Following the incident, Rackspace said it’s shuttering its hosted Exchange service. It’s not clear, though, if Rackspace paid the ransom or not, since the Play leak site doesn’t yet list the data. Read more: OWASSRF: CrowdStrike Identifies New Exploit Method for Exchange Bypassing ProxyNotShell Mitigations
Cops hacked thousands of phones. Was it legal?
Encrochat, a highly-customized and encrypted Android phone service used almost exclusively by criminals, was secretly hacked by European police and became an intelligence goldmine on thousands of organized criminals. But the methods of the secret police-led hack, which led to the arrests of hundreds of people and crime rings dismantled, are under scrutiny, and are resulting in significant legal challenges and setbacks to these cases. Given that these encrypted devices were ultimately hacked, and that many European countries don’t allow or highly restrict the use of intercepted data in court, things aren’t going so well for the prosecutors, reports Wired. Encrochat isn’t the only case. If you recall, Anom, another encrypted phone service used by crims, was also secretly hijacked and taken over by the FBI — and they’re facing similar court rulings because the severity of the alleged crimes didn’t justify the means.
First LastPass, now Slack and CircleCI have confirmed hacks
It’s been a bumpy start to 2023. Software testing company CircleCi confirmed on Wednesday that it was breached in December and warned customers to “immediately rotate any and all secrets” stored in CircleCi, in a blog about the incident. The news comes shortly after Slack confirmed its GitHub account was compromised and intruders downloaded private code repositories — a compromise similar in style to LastPass’ first breach in August, which as we know unraveled by Christmas. Still, Slack said in its opaque statement that there’s nothing to worry about. Read more: CircleCI security alert: Rotate any secrets stored in CircleCI (Updated Jan 7)
Russian hackers targeted U.S. nuclear scientists
A Russian hacking unit is accused of targeting U.S. nuclear scientists and labs, according to a Reuters investigation. The hacking unit, previously dubbed “Cold River” by Google researchers, created fake login pages for each targeted U.S. lab and emailed scientists in the hope of stealing their passwords. Cold River was previously linked to a hack-and-leak operation involving the former head of British spy agency MI6. But missteps by the Cold River crew in recent years allowed analysts to identify one of its members, a 35-year-old IT worker and bodybuilder called Andrey Korinets from a town north-east of Moscow, who used his personal emails (or emails connected to him) to set up the hacking group’s infrastructure. Incredible work here. Read more:
- Exclusive: Russian hackers targeted U.S. nuclear scientists
- Update on cyber activity in Eastern Europe
How do you know when macOS detects and remediates malware?
This blog looks at how macOS detects and blocks malware using the in-built XProtect system — and some valid criticisms of how it could improve. Read more: How do you know when macOS detects and remediates malware?


The revamped NSA museum opens with displays of former nuke secrets and spy artifacts
NPR’s cybersecurity correspondent @jennamclaughlin has a fantastic visual (and audio) package exploring the NSA’s new museum, featuring some of the most important and critical spy, intelligence, defense and military, and codebreaking technologies of recent history — even if it’s the NSA’s sanitized version. Read more: The revamped NSA museum opens with displays of former nuke secrets, spy artifacts
Guardian shutters office after ransomware attack
The ransomware attack on the London-based newspaper The Guardian continues on, with the outage reportedly affecting everything from its office Wi-Fi network to the check-outs in the staff canteen. The incident, which began on December 20, was followed by a memo to employees saying its London office will stay closed until January 23. Staff said the newspaper “nearly missed its payroll.” Staff have also voiced concerns that production data was either lost, or potentially compromised, by the hack. Read more: A mysterious cyberattack has shuttered the Guardian’s office for a month
Twitter’s latest security headache
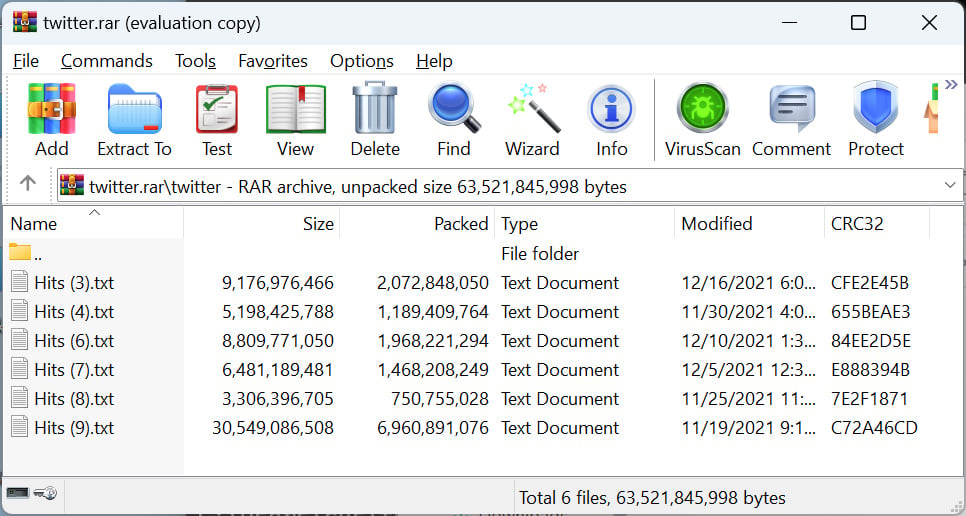
Some 200 million Twitter users’ email addresses were leaked online this week after weeks of back-and-forth about claims of an alleged breach. The scraped data set is the first major security incident of Elon Musk’s tenure as Twitter CEO, even if the data was limited to just email addresses and not phone numbers as feared. That said, it’s a major headache (and likely concern) for pseudonymous accounts whose efforts to keep their identities hidden may have been compromised as a result of this leak, and as such it’s unsurprisingly drawing the attention of regulators. The data is searchable in Have I Been Pwned.
Updated on 2023-01-06
If the security posture is not strong enough, a cyberattack against a firm can spill onto entities related to the victim. This is something that hundreds of U.S. counties are dealing with, owing to a cyberattack at a third-party vendor. If you have applied for a job at Five Guys, your data might have been compromised, revealed the burger chain. In other news, cryptocurrency losses pile up year-on-year as cybercriminals get busy hacking. Here are the top 10 highlights from the past 24 hours.
More highlights from the past 24 hours
Five Guys, the U.S. burger chain, disclosed a data breach that impacted the names, Social Security numbers, and driver’s license numbers of job applicants.
The Saint Gheorghe Recovery Hospital, Romania, revealed suffering a ransomware attack in December 2022, which impacted medical activity. The actors demanded a ransom of 3 Bitcoins. Read more: Spital luat ostatic de hackeri
New research found that cryptocurrency hacks surged in 2022, leading to a $3.7 billion in loss – a 58% increase from 2021. Over 95% of every cryptocurrency theft was caused due to hacks. Read more: CRYPTO LOSSES IN 2022 Prepared by Immunef
Confidential data, including students’ SEN info, staff pay scales and contract details, and pupil passport scans, from 14 U.K schools was leaked online by hackers from attacks in 2022.
A study of the top 100 breaches from July 2021 to July 2022 disclosed that hackers aimed for PII 42.7% of the time, followed by source code, proprietary information, medical information, and others. Read more: More Lessons Learned from Analyzing 100 Data Breaches
The NIST issued its final version of its guidance—NIST Interagency Report 8401—on applying the cybersecurity framework to the ground segment of space operations, especially satellite command and control. Read more: Satellite Ground Segment: Applying the Cybersecurity Framework to Satellite Command and Control [PDF]
Cloud security vendor Netskope raised $400 million in debt financing from Morgan Stanley to expand its SASE platform. Read more: World’s Premier Investors Line Up to Partner with Netskope as the SASE Security and Networking Platform of Choice
Updated on 2023-01-05
What secrets are you keeping in your CircleCI? Threat actors might already know them – warned the CI/CD platform. A popular hacking forum was found selling millions of Twitter user profiles for a minimal amount. Did Volvo Cars get breached? A threat actor says so. Here are the top 10 highlights from the past 24 hours.
More highlights from the past 24 hours
A dataset containing the email addresses of 200 million Twitter profiles was put up for sale, on the Breached hacker forum, for $2. It was released as a RAR archive with a size of 59GB.
French music streaming service Deezer revealed suffering a data breach that potentially compromised the dates of birth, email addresses, IP addresses, and others of over 225 million users.
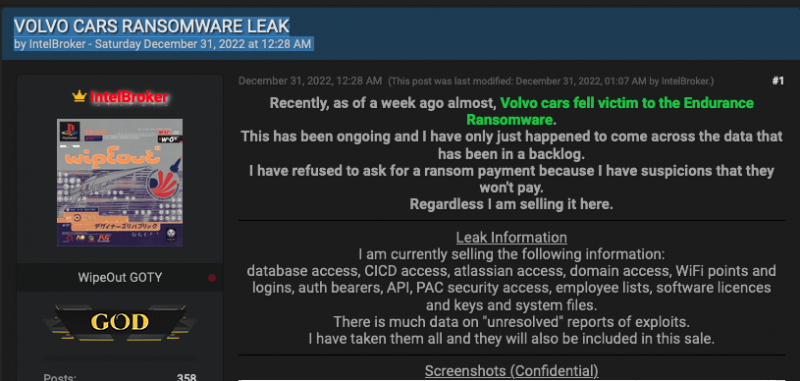
A hacker, named IntelBroker, has put up for sale data allegedly stolen from Volvo Cars, following a ransomware attack, dubbed Endurance, in December 2022. The data includes existing and future vehicle models, employee information, and others.
ThreatFabric spotted a new version of SpyNote, an Android malware, targeting financial institutions such as HSBC U.K., Nubank, Kotak Mahindra Bank, and Deutsche Bank. Read more: SpyNote: Spyware with RAT capabilities targeting Financial Institutions
Swansea Public Schools, Massachusetts, suffered a ransomware attack that shut down its networks, forcing it to cancel classes. No other details have been released yet.
A social platform for the online cricket community, Cricketsocial[.]com, was found exposing over 100,000 private customer data and credentials, owing to an unsecured AWS bucket.
New report by CloudSEK revealed that cyberattacks against the government sector surged by 95% in H2 2022 compared to the same period in 2021. Hacktivist activity accounted for 9% of all attacks, followed by ransomware attacks at 6%. Read more: Unprecedented Increase in Cyber Attacks Targeting Government Entities in 2022 [PDF]
Check Point detected a new campaign by Blind Eagle, aka APT-C-36, targeting Ecuador with an upgraded version of QuasarRAT and other modified tools. Read more: BLINDEAGLE TARGETING ECUADOR WITH SHARPENED TOOLS
Symantec detected the Bluebottle threat actor targeting Francophone nations in Africa, in a campaign running from at least July 2022 to September 2022. Read more: Bluebottle: Campaign Hits Banks in French-speaking Countries in Africa
Twitter data leak
On Christmas, a threat actor put up for sale the public and private details of more than 400 million Twitter users that they claimed to have scraped off the site using a vulnerability in the platform’s API. This week, the details of more than 235 million Twitter users were leaked online and are accessible to anyone.
Potsdam cyberattack
The German city of Potsdam took its IT network offline on December 29 following a warning from the security team of the state of Brandenburg that the city’s network was being targeted with a brute-force attack. Officials said they plan to reconnect their network to the internet next week following a series of security audits. Read more: Umfangreiche Sicherheits-Tests nach präventiver Abschaltung der Internetverbindungen
3Commas cyber-heist
The CEO of the 3Commas cryptocurrency platform has confirmed that a hacker has stolen the API keys of its users after multiple victims have claimed over the past two months that they had unauthorized access to their cryptocurrency accounts via the 3Commas platform and lost assets worth millions of USD. After news of some of these hacks started to become public, the hacker leaked 10,000 API keys on Pastebin as a way to advertise a larger batch of 100,000 keys. 3Commas came under heavy criticism for denying the hack for two months, claiming that users were phished rather than admitting a breach on its side. Read more: Notice on API data disclosure incident
T-Mobile breach settlement
Users who’ve been affected by T-Mobile’s 2021 data breach are eligible to receive up to $100 from a $350 million settlement. The catch—they have weeks to make a claim.
LastPass gets sued
LastPass has been sued over its disastrous handling of the August 2022 security breach, which resulted in a second breach in December 2022, and then in the theft of encrypted password vaults. Read more: Doe, Individually and on behalf of all others similarly situated v. LastPass US LP (1:23-cv-10004)
Deezer data breach
Back in 2019, a third-party contractor was hacked and allowed a threat actor to collect the data of almost 230 million Deezer users. The company confirmed the hack in November, weeks after a threat actor began selling the old data. The data has now leaked and was indexed on Have I Been Pwned. Read more: Third Party Data Breach
Five Guys breach
US fast food restaurant chain Five Guys has disclosed a data breach that took place in September 2022. The company, which runs more than 1,700 locations across the US, said the incident “involved unauthorized access to files on a file server.” A class-action lawsuit is being prepared—because, of course it is. Read more:
- Five Guys Consumer Notification Letter
- Five Guys Data Breach Investigation
Meta fined in the EU
EU officials have fined Meta a total of €390 million (€210 million for Facebook and €180 million for Instagram) after the company was found to have bypassed GDPR through clauses in its terms of service and used its EU users’ personal data for targeted advertising without their explicit consent. EU officials have also given Meta three months to become GDPR compliant. Read more: Data Protection Commission announces conclusion of two inquiries into Meta Ireland
Google spam call warning
Google has announced that its Google Voice service will be adding a “suspected spam caller” warning to calls the company’s service believes are automated spam. Read more: Get enhanced spam protection through automatic labeling of suspected spam calls in Google Voice

Twitter advertising
Twitter has lifted its ban on political advertising—because the site wasn’t a trash heap of propaganda, and we all needed more misleading tweets about that garbage in our life.
Firefox browser detection
Mozilla will change the Firefox user-agent string to avoid situations where the browser is accidentally detected as Internet Explorer 11 and blocked from loading certain websites. Read more:
- Remove the frozen `rv:109.0` IE11 UA workaround after Firefox reaches version 120 (desktop and Android)
- Wegen des Internet Explorers 11: Mozilla ändert User-Agent von Firefox
Russia’s Android clone
Major Russian companies like VK, Yandex, Sberbank, and Rostelecom are reportedly planning to create their own mobile operating system to be used inside the country. According to Kommersant, the new OS will be based on the Android open-source project, will be used for devices in the Russian consumer market, and will be different from Rostelecom’s Aurora OS, which will target Russia’s enterprise and government sectors. Read more: Ничто человеческое Android не чуждо
Ukraine dismantles another bot farm
Ukraine’s Cyber Police said it dismantled another Russian bot farm operating inside its borders. The group operated out of 13 locations using more than 100,000 SIM cards and 1.5 million online accounts to spew Russian propaganda inside Ukraine and abroad. The crackdown marked the seventh time in 2022 that Ukrainian officials have gone after Russian bot farms operating inside Ukraine, after similar operations in February (18,000 bots), March (100,000 bots across five bot farms), August (1,000,000 bots), September (7,000 bots), and October (50,000 bots), twice (10,000). Read more: Кіберполіція провела загальнонаціональну операцію з припинення діяльності ворожих ботоферм
Poland warning
The Polish government has warned of impending cyber-attacks carried out by Russian hackers because of the country’s active support of Ukraine. Read more: Russian cyberattacks
Propaganda pact
Files hacked and leaked from the VGTRK Russian state broadcaster show that Russian and Chinese government officials and media executives have signed bilateral agreements to pick up each others’ fake news coverage and narratives in order to boost their anti-western propaganda. Read more: HACKED RUSSIAN FILES REVEAL PROPAGANDA AGREEMENT WITH CHINA
US court ruling on ransomware and insurance
The Ohio Supreme Court has ruled that classic insurance policies do not cover cyber-security incidents such as ransomware attacks for which dedicated cyber-insurance policies should be used. The court ruled that only “direct physical loss” or “direct physical damage” are covered by classic insurance policies.
RedZei
William Thomas has discovered a new threat actor. He named the group RedZei, which he said engages in scam calls from Chinese-speaking fraudsters targeting Chinese international students at universities in the UK. Read more: RedZei – Chinese-speaking scammers targeting Chinese students in the UK
Data leak site on I2P
The BianLian group has become the first ransomware gang to establish a data leak portal on the I2P network.
Pupy RAT campaign
K7 researchers have broken down a malware distribution campaign that deployed the Pupy RAT via Windows Error Reporting, a legitimate tool found on all Windows installations. Read more: Pupy RAT hiding under WerFault’s cover
MBR locker campaign
An MBR locker campaign is hitting Chinese users. The malware is currently being distributed via local free software download sites. Read more: 乱下载软件致MBR锁机,逆向分析自救
New npm malware
Twenty new malicious npm packages were recently discovered on the official npm portal. Check out GitHub’s security advisory portal for details.
Google Cloud threat analysis
In its quarterly threat report [PDF], Google Cloud said that threat actors had diversified their methods of breaching customer accounts, with API compromise accounting for a large subset of intrusions in Q3 2022 (20%), with the method being rarely used before this quarter. The use of weak or no credentials to protect accounts remained the top way of entry in most intrusions (41% in Q3, down from 57% in Q2).
OrBit dropper
Stormshield researchers have a technical analysis of the OrBit Linux malware, first spotted last year by Intezer. Read more: OrBit: advanced analysis of a Linux dedicated malware
Hornet ransomware
Rixed Labs researchers have published a technical analysis of the Hornet ransomware. Read more: A brief analysis of Hornet Ransomware
CatB ransomware
On the same note, Minerva Labs has a similar report on the new CatB ransomware, which they found to be using a two-year-old DLL hijacking technique to evade detection and a ransom note cobbled up with parts from other ransomware families. Read more: New CatB Ransomware Employs 2-Year Old DLL Hijacking Technique To Evade Detection
Confucious APT
NSFocus researchers have analyzed recent operations of the Indian-based Confucious APT that have targeted the armed forces in the Multan area of Pakistan. Read more: APT组织CONFUCIUS针对巴基斯坦IBO反恐行动的网络攻击事件分析
Transparent Tribe
Qihoo 360 researchers have a report on the recent operations of the Pakistani APT Transparent Tribe and its recent use of a new remote access trojan (RAT). Read more: APT-C-56(透明部落)利用外贸链接伪装文档攻击分析
“A simple RAT was used in this attack, including screen monitoring, keyboard monitoring, and network transmission functions. We suspect that it is an undiscovered component in the operation.”
Android security updates
…for January 2023 are out! Read more: Android Security Bulletin—January 2023
Breaking 2048-bit RSA
In a recently published study, a team of Chinese academics claims that quantum computers currently available on the market are theoretically capable of breaking the 2048-bit RSA encryption algorithm. As Bruce Schneier points out, the paper has not been proven in practice just yet. Read more:
- Factoring integers with sublinear resources on a superconducting quantum processor
- Breaking RSA with a Quantum Computer
Mastodon DDoS protection
Apparently, it’s quite trivial to determine the real IP address of a Mastodon server, even if it’s behind Cloudflare’s proxy network. Cool, let the DDoS attacks begin, then. Read more: Detecting the real IP of a Cloudflare’d Mastodon instance
Google Home smart speaker vulnerability
Bug hunter Matt Kunze has published details on a vulnerability that could be used to access the microphone of Google Home smart speakers over the internet and turn them into remote listening devices (among other things). Google awarded the researcher $107,500 as a bug bounty for his report. Read more: Turning Google smart speakers into wiretaps for $100k
ENLBufferPwn
Spanish software developer has discovered a vulnerability in the firmware of Nintendo consoles such as 3DS, Wii U, and Switch. Named ENLBufferPwn (CVE-2022-47949), the vulnerability “allows remote code execution in a victim console by just having an online game session with an attacker.” Apparently, Nintendo has refused to acknowledge the issue (no surprise here) and did not release security patches.
Twitter whistleblower update
Former Twitter security chief Peiter Zatko has joined cybersecurity firm Rapid7 as a consultant.
New tool—dnstwist
Belgian security researcher Niels Hofmans has open-sourced dnstwist, an online tool that can scan for lookalike and IDN domains that could be abused for phishing attacks.
Updated on 2023-01-04
LockBit added a rail and locomotive company to its leak site in August 2022. The company has finally disclosed the incident to the public, although not stating what kind of cyberattack it was. As students are just returning to schools and colleges, a ransomware group already breached and leaked the data of an Australian university. In other news, the Raspberry Robin worm is back with new upgrades. Read along for more from cyberspace.
More highlights from the past 24 hours
A misconfigured Elasticsearch database belonging to a Californian ERP software provider is currently exposing the personal data of over half a million Indian job seekers. Read more: Top ERP Firm Exposing Half a Million Indian Job Seekers Data
According to the NCSC-U.K, the NHS topped the list of most impersonated U.K government organizations in email scams in 2022, followed by TV Licensing, HMRC, and others. Read more: Phishing: Spot and report scam emails, texts, websites and calls
Maybank, the Election Commission, and satellite broadcaster Astro, in Malaysia, suffered an alleged data breach that impacted 13 million citizens. Investigation is ongoing while Maybank denied the incident.
A new shell script compiler (shc) Linux malware was found installing XMRig miner, deployed alongside a Perl-developed DDoS IRC Bot, by exploiting inadequately managed Linux SSH servers. Read more: Shc Linux Malware Installing CoinMiner
IT service management platform Matrix announced the acquisition of value-added cybersecurity solutions distributor Zebra Technologies for $18.5 million. Read more: Matrix acquires Israel’s Zebra Technologies
Updated on 2023-01-02
Wishing you all a very Happy New Year! However, the cybersecurity landscape is still hounded by dark clouds of cyberattacks. The Bristol Community College suffered a ransomware attack that left quite some disruption in its wake. In the data breach section, the Indian arm of a Japanese automaker suffered a breach that is under further investigation. New year, new tactics – seems to be the motto of the ALPHV ransomware group. Read along to know what cooked in cyberspace over the weekend.
More highlights from the past 24 hours
A ransomware attack against the computer systems of Bristol Community College affected onsite internet and network functions such as email, shared information systems, and Teams. Read more: Bristol Community College’s computer systems hacked in ransomeware attack

Toyota Kirloskar Motor (TKM) reported a data breach that potentially compromised the personal detail information of some of its customers. The extent of the data breach is being investigated. Read more:
New research by Jama Network disclosed that the medical records of 42 million Americans are being sold on the dark web, since 2016. Read more: Trends in Ransomware Attacks on US Hospitals, Clinics, and Other Health Care Delivery Organizations, 2016-2021
Data security software vendor Netwrix announced the acquisition of Privileged Access Management (PAM) technology firm Remediant, for an undisclosed sum, an early-stage startup working on technology in the PAM category.