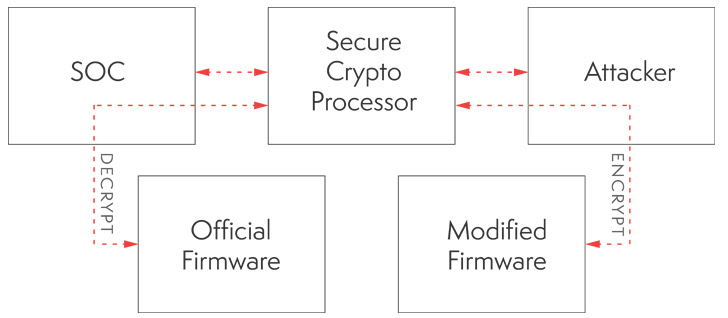
An architectural vulnerability in more than 100 models of Siemens SIMATIC and SIPLUS S7-1500 programmable logic controllers (PLCs) could be exploited to install firmware and bypass all protected boot features. Because of the nature of the flaw, it cannot be fixed with a software patch. Siemens notes that exploiting the flaw requires physical access to vulnerable devices; the company “recommends [that users] assess the risk of physical access to the device in the target deployment and to implement measures to make sure that only trusted personnel have access to the physical hardware.
Note
- There are really only two options here – either limit physical access, or purchase replacement units which have the improved secure boot (with an immutable root of trust) which resolve this flaw. As exploiting the flaw requires physical tampering, you could consider tamper indicators, but make sure you are checking them. Consider the costs of physical restrictions, with monitoring, versus replacements.
- These bugs are probably the worst-case scenarios for everyone involved. Very few organizations will be replacing their PLCs universally. Given this, organizations must accept that it’s a risk whenever someone touches those PLCs. It will be curious if we ever read about an insider attack with these controllers.
- This vulnerability serves as a reminder that organizations regularly review all aspects of their information security program. In this case both physical and personnel security processes are a primary focus for defensive actions based on this vulnerability.
Read more in
- SSA-482757: Missing Immutable Root of Trust in S7-1500 CPU devices
- Critical Architectural Vulnerabilities in Siemens SIMATIC S7-1500 Series Allow for Bypass of All Protected Boot Features