Table of Contents
Updated on 2022-12-04: Android phone makers’ encryption keys used in malware
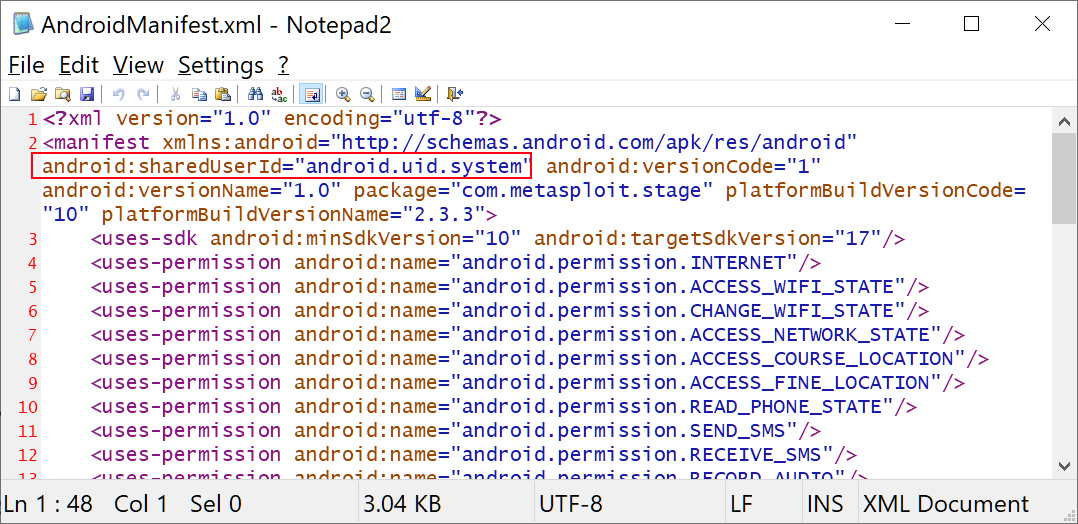
It’s never good when private keys are leaked or stolen, but even worse when they’re reused for malware. But that’s what happened with Android device makers Samsung and LG. @maldr0id found that “platform certificates” used to verify legitimate third-party Android system apps developed by device manufacturers like Samsung and LG had been stolen and used to sign malware, essentially allowing malware to run as if it was a highly privileged Android system app. Not good! Google said the Android device makers had rolled out mitigations and rotated their keys, ending the threat. There have been “no known security incidents,” Samsung said, with an emphasis on “known.” That’s more than what LG said, which was sweet nothing. Read more: Principles for Secure Software Distribution: Lessons from Leaked Android Platform Signing Keys
Updated on 2022-12-02
Several platform certificates, belonging to LG Electronics, Revoview, Mediatek, and Samsung Electronics, were found being abused by threat actors to sign malicious Android apps. Read more: Samsung, LG, Mediatek certificates compromised to sign Android malware
Overview: Android Platform Certificates Stolen, Used to Sign Malicious Apps
According to Google, platform certificates used by original equipment manufacturers (OEMs) of Android handsets have been compromised (stolen) and used to validate malicious Android apps. Google says that “OEM partners promptly implemented mitigation measures as soon as we reported the key compromise. End users will be protected by user mitigations implemented by OEM partners.”
Note
- This story is sad for a number of reasons: First of all, there appears to be no good way to replace the certificates or revoke them. The only thing that apparently can be done is to not allow applications signed with these certificates in the Google play store. Secondly, the malware signed with these certificates has been circulating for years. It was just recently discovered that the certificates used are Android platform certificates. Third: There is no word from the affected companies about how the certificates ended up being used to sign malware. And… the certificates will not expire until well into the 2030s.
- Platform certificates are kinda like skeleton keys that can open every lock (OK, even I’m not old enough to ever have actually used a skeleton key…) Their use should obviously be minimized, and they need to be really, really protected. Looks like neither of these principles were followed by the Android OEMs. The fact that multiple OEMs offer Android phones and tablets has helped Google gain market share over Apple but this (and the “patch gap” issues) point out the risks and the fact that Google needs to invest more in making sure the Android ecosystem is trustable.
- The platform certificate allows the OS to run with high levels of privilege, so any applications signed with those stolen credentials can also run at those increased privilege levels without user consent. OEM’s have been pushing out updated certificates over the air; make sure that you keep your devices updated to capture these new certificates. Train users to review installed applications, removing those they don’t use, and revisiting/reducing the permissions on those they do to.
- Without going into much detail, we have seen code-signing certificates in the wild left in an unsecured state. This is the worst-case scenario for many platforms. The operating systems use certificates as trust anchors, so make sure you properly secure them.
- Certificates are public meta data about public keys; copying them is not “stealing.” They cannot be used to sign. It is the private half of the key-pair that is used to sign and that has been stolen. Signing keys should not be kept online when not in use.
Read more in
- Issue 100: Platform certificates used to sign malware
- Android Phone Makers’ Encryption Keys Stolen and Used in Malware