Updated on 2023-01-09: Amazon S3 is Now Encrypting New Objects by Default
Amazon Simple Storage Service (Amazon S3) now encrypts all new buckets by default. S3 will apply server-side encryption for all new objects unless users specify otherwise. Users can currently choose between three encryption options: S3 default encryption (SSE-S3, the new default), customer-provided encryption keys (SSE-C), or AWS Key Management Service keys (SSE-KMS).
Note
- Nice move by Amazon. Compare this to full disk encryption on a laptop: It helps if the laptop gets stolen, but doesn’t help if someone can guess your password. You still need to be careful who has access to your data. Client-side encryption should be preferred (and AWS has great tools for that), but it is more work, so only do it to customer data if you care about customer privacy.
- The “crypto done righ, good; crypto done poorly, bad” thread is pretty obvious in this issue of NewsBites. Amazon makes it easy but not trivial to do S3 stored data encryption right. Once you get it (and “it” includes authentication) right for new storage, you can also retroactively encrypt previously stored data.
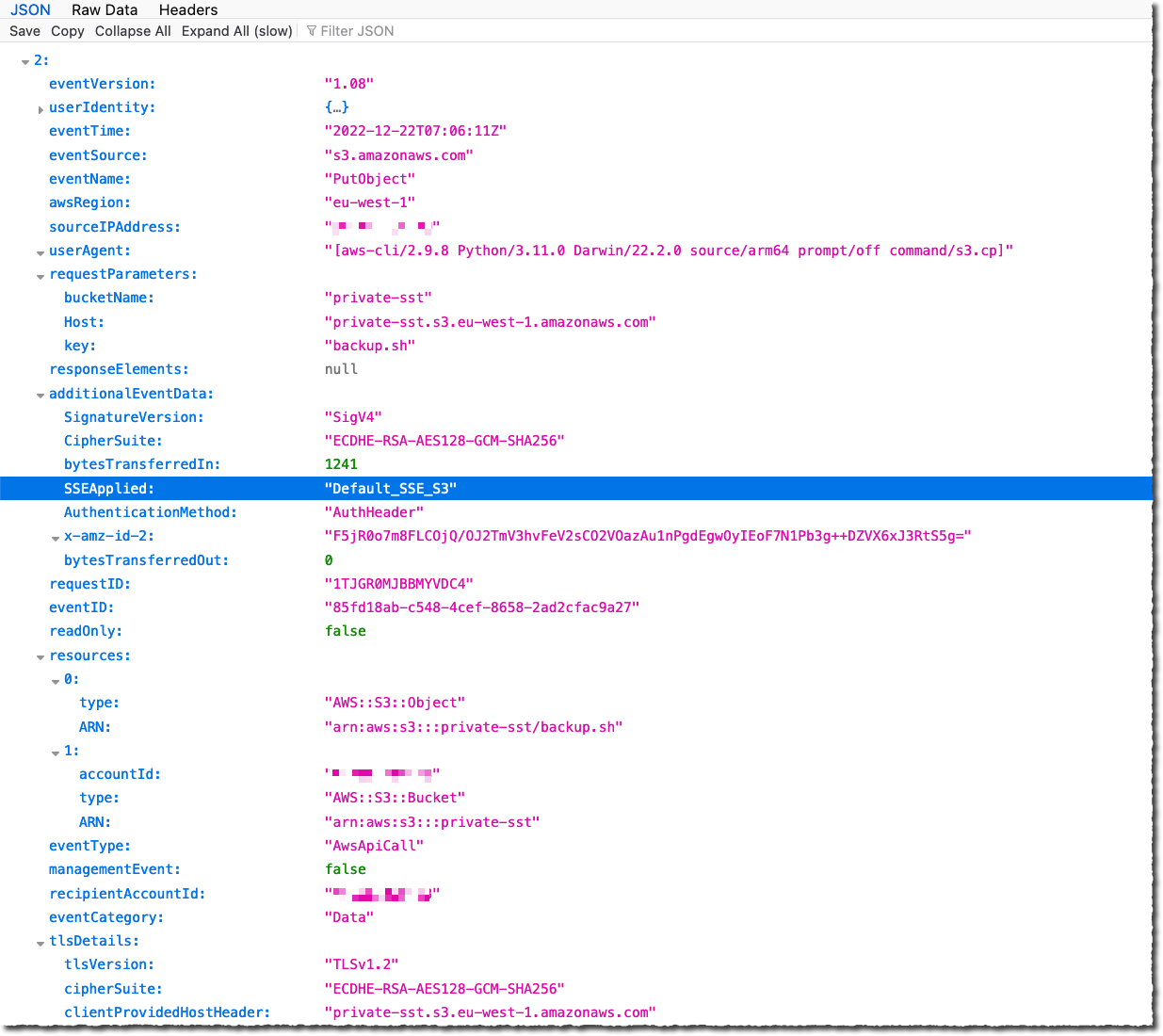
- Cloud services have made it increasingly easy to encrypt everything at rest, don’t pass go, select your key management option, and enable it. You can verify the encryption status in the AWS CloudTrail event logs, and soon you’ll have more information in other tools like the AWS Management Console, AWS S3 Inventory, etc. Best of all, there is no added cost for the default encryption on S3.
- An easy change that will have dramatic cybersecurity results – moving from opt-in to opt-out by default results in encrypted S3 buckets. This change has the added benefit of automating one of the compliance checks required by cybersecurity audits.
Overview: New AWS defaults
Amazon says that starting January 5 this year, all data stored in AWS S3 servers is now encrypted by default. Server-side data encryption has been available to S3 customers since 2011, but the feature has only been optional until now. Amazon also plans to change another AWS default in April, when all new S3 servers will block access to stored data by default. Until now, all AWS S3 servers were open to public access unless administrators took intentional steps to set the servers private. Read more:
- Amazon S3 Encrypts New Objects By Default
- Advanced Notice: Amazon S3 will automatically enable S3 Block Public Access and disable access control lists for all new buckets starting in April 2023